 NEWS
NEWS
 NEWS
NEWS
 NEWS
NEWS
![]() Today’s businesses not only face threats from outside cyber predators, but are at risk from inside jobs as well. Earlier this year we learned about the risks of security systems built around a forensic model. When activity can only be traced after it has occurred, it is usually too late (i.e. the Edward Snowden document leaks.) In order for the Enterprise to maintain stability from the inside out, the type of security a business is critical. Of course there are many security options and countless approaches, but the type of security an organization employs can actually be detrimental to its network stability. The pace of today’s enterprise calls for network protection that allows 100% visibility and continuous 24/7 analysis in real-time.
Today’s businesses not only face threats from outside cyber predators, but are at risk from inside jobs as well. Earlier this year we learned about the risks of security systems built around a forensic model. When activity can only be traced after it has occurred, it is usually too late (i.e. the Edward Snowden document leaks.) In order for the Enterprise to maintain stability from the inside out, the type of security a business is critical. Of course there are many security options and countless approaches, but the type of security an organization employs can actually be detrimental to its network stability. The pace of today’s enterprise calls for network protection that allows 100% visibility and continuous 24/7 analysis in real-time.
![]() The need for a real-time monitoring model fills in the flaws of the old standards. More and more things are shifting to real-time security models that gather machine data from the environment and analyzes this information for security threats, bringing security issues to light before it’s too late. The way that works of course is a case study in Big Data – analytics at velocity, variety, and volume. One issue however is that while Big Data is not a new concept, many businesses are still struggling to manage their data effectively. Hadoop for example, was not written with security in mind, and to date, the open source Hadoop community has yet to focus on addressing this critical gap. Enterprise organizations with data at risk, including those that must adhere to regulatory compliance mandates like the finance and healthcare sectors are especially at cause for concern.
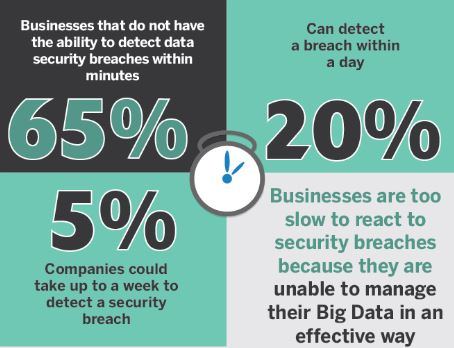
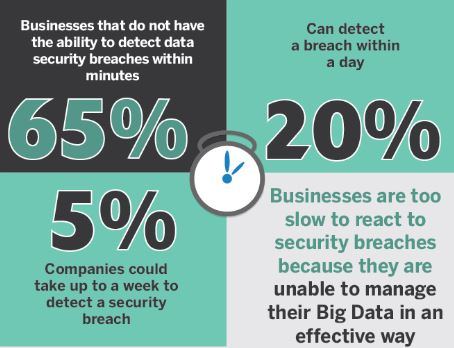
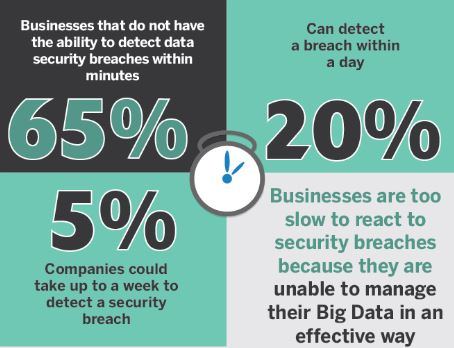
The need for a real-time monitoring model fills in the flaws of the old standards. More and more things are shifting to real-time security models that gather machine data from the environment and analyzes this information for security threats, bringing security issues to light before it’s too late. The way that works of course is a case study in Big Data – analytics at velocity, variety, and volume. One issue however is that while Big Data is not a new concept, many businesses are still struggling to manage their data effectively. Hadoop for example, was not written with security in mind, and to date, the open source Hadoop community has yet to focus on addressing this critical gap. Enterprise organizations with data at risk, including those that must adhere to regulatory compliance mandates like the finance and healthcare sectors are especially at cause for concern.
Compliance mandates are known for many things, including the checklists they can generate for an organization. When you’re integrating a novel solution like Hadoop, it’s certainly important to verify that all the technical requirements are satisfied. So it’s interesting to note that if you’re thinking about bringing a Hadoop-based solution that cluster management capabilities be a part of that solution and that centralized log management is available in order to capture events for compliance audits. It can also mean that a fine-grained role-based access control approach needs to be implemented to meet compliance, and that your existing policy enforcement framework such as LDAP/AD can be integrated. The thing to know is it’s not as easy as throwing Big Data technology at security and expect it to work.
Ineffective data management can leave gaps that cyber predators are programmed to seek out. As a result, security breaches can take place right under a company’s nose, leaving a business stunned and left to deal with the aftermath. Thus, an inadequate network can leave a company at risk for Denial of Service (DOS) or Distributed Denial of Service (DDoS), loss of company information, financial losses due to customer retention and claims against the business.
A true Network Monitoring System with 100% visibility and analysis is built with the ability to protect everything in your environment including Big Data itself while keeping private information secure, and gaining better insight into critical business issues. One example is the Zettaset Orchestrator which is not a Hadoop distribution, but operates as an independent management software layer that works with open source distributions. The Zettaset solution can help IT teams achieve the level of enterprise security and regulatory compliance they need in a cluster environment, while reducing IT resource requirements by automating administrative and management processes that, with open source distributions, typically involve time-consuming manual configuration. While no network is un”breach”able, visibility in real-time and the implementation of automation can drastically reduce a businesses vulnerability to cyber-attacks.
If your business can embrace the analysis, storage and management of big data security; it will be better protected from cyber breaches. If you’re considering an upgrade to your network, here are a few tips on how to implement a real-time network model:
Contributing Editor: John Casaretto
Support our mission to keep content open and free by engaging with theCUBE community. Join theCUBE’s Alumni Trust Network, where technology leaders connect, share intelligence and create opportunities.
Founded by tech visionaries John Furrier and Dave Vellante, SiliconANGLE Media has built a dynamic ecosystem of industry-leading digital media brands that reach 15+ million elite tech professionals. Our new proprietary theCUBE AI Video Cloud is breaking ground in audience interaction, leveraging theCUBEai.com neural network to help technology companies make data-driven decisions and stay at the forefront of industry conversations.