 NEWS
NEWS
 NEWS
NEWS
 NEWS
NEWS
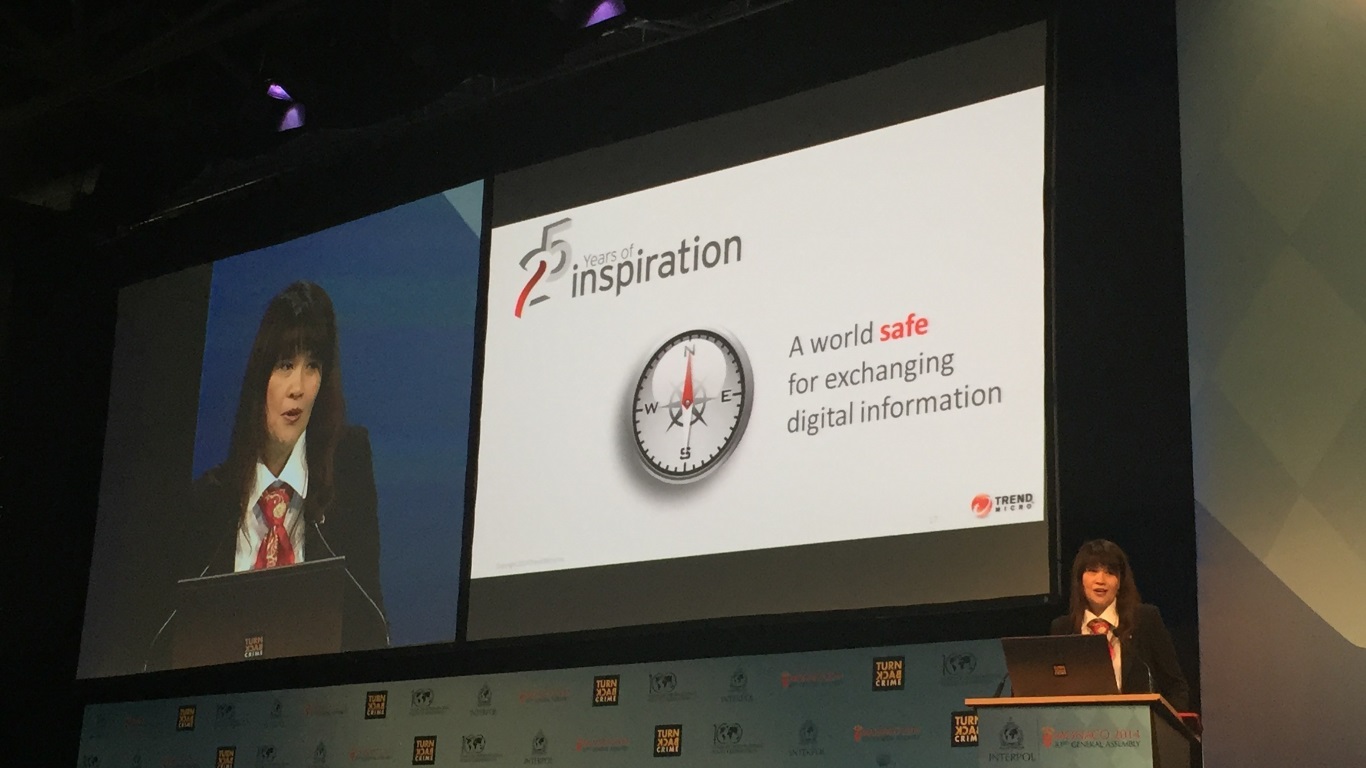
Trend Micro CEO Eva Chen
Cybercriminals are using smarter tactics to try and ‘phish’ for netizen’s all important private credentials, employing proxy servers to intercept communications rather than serving up clumsy-looking, fake websites to try and trick people.
Traditionally, phishing scams involve setting up a fake website – for example a fake login page for your regular bank – and hope that people will unwittingly enter their user name and password to try and login. Users are often directed to those sites by way of spam emails that purport to be from the bank and contain a link to the aforementioned dodgy site.
But unfortunately for the cyber-crims, a growing number of netizens are switched on to this kind of scam. Fake sites are often easy to spot, and so the hackers have devized a better way to ensure they get what they’re phishing for, reports Trend Micro.
Instead, victims are being redirected to fake servers that fetch the genuine login page from your bank or online service, which is far more convincing. For certain sites, like those selling items online, the thieves can even edit the page to reduce prices for certain items to make it even more tempting to enter your credentials.
According to web security firm Trend Micro Inc., the technique allows cybercriminals to create the perfect copy of any website, because they don’t actually need to copy anything at all. “Instead, the phishing page only contains a proxy program, which acts as a relay to the legitimate site,” Trend Micro explains in its blog post. “Only when any information theft needs to be carried out are any pages modified. The owners of the legitimate site would find it very difficult to detect these attacks against their customers.”
Trend Micro has dubbed the new tactic as “Operation Huyao”, which is Chinese for “monstrous fox”. It chose the name because the cybercriminals using the tactic appear to be located in China. Apparently, the tactic is almost entirely reliant on people not noticing that the HTTPS website isn’t the HTTPS site they think they’re on. And how many people are that diligent?
The tactic has already been used against at least one Japanese shopping site, and the worrying thing is they didn’t use standard phishing tactics either. Instead, they used ‘black hat’ SEO tricks to get the compromised site up to the top of search engine results when Japanese netizens searched for certain products.
Support our mission to keep content open and free by engaging with theCUBE community. Join theCUBE’s Alumni Trust Network, where technology leaders connect, share intelligence and create opportunities.
Founded by tech visionaries John Furrier and Dave Vellante, SiliconANGLE Media has built a dynamic ecosystem of industry-leading digital media brands that reach 15+ million elite tech professionals. Our new proprietary theCUBE AI Video Cloud is breaking ground in audience interaction, leveraging theCUBEai.com neural network to help technology companies make data-driven decisions and stay at the forefront of industry conversations.