 SECURITY
SECURITY
 SECURITY
SECURITY
 SECURITY
SECURITY
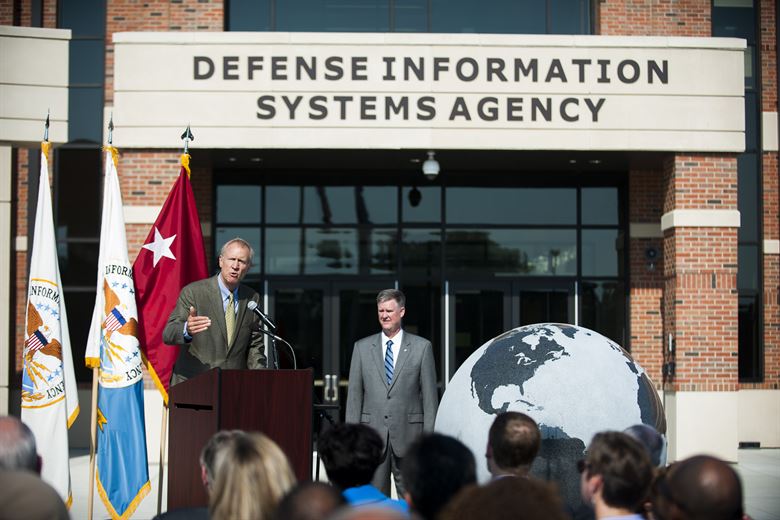
A data breach has hit the Defense Information Systems Agency, the U.S. Department of Defense agency tasked with providing information technology and communications support to the White House, Secretary of Defense, military services and combat commands.
The personal data of about 200,000 people, including names and Social Security numbers, may have compromised, though the agency said it has no evidence data was stolen. The breach was disclosed in a letter to those who were affected, Reuters reported today.
Details are slim on exactly what took place, but the breach occurred between May and July 2019 on a system hosted by DISA. When asked for direct comment by the BBC, a DOD spokesperson did not provide any further details but did confirm that the agency was notifying those affected, adding, “DOD networks are under attack daily and the department maintains an active posture to thwart those attacks.”
Given that the agency is responsible for secure communications at the White House and for military commands, concerns have been raised that the data breach may have affected national security.
“The details of the reported breach are pretty obscure,” Ilia Kolochenko, founder and chief executive officer of web security company ImmuniWeb, told SiliconANGLE. “At first glance, just one system hosting employee data had been breached and, if so, it seems to be a comparatively insignificant security incident of minor importance.”
Kolochenko said an in-depth investigation should be conducted. “Frequently, nation-state attackers commence their attacks by breaching the weakest link accessible from the internet and then silently propagate to all other interconnected systems in a series of chained attacks,” he said. “Worse, access to personal data of the agency staff greatly facilitates a wide spectrum of sophisticated spear-phishing and identity theft attacks capable of bypassing virtually any modern layers of defense.”
Chris Morales, head of security analytics at cybersecurity firm Vectra AI Inc., noted the lack of details about the breach.
“If the DOD can be compromised, that anyone can,” Morales said. “Every network is complex and human error is common regardless of the level of organization.”
Suggesting that this could be a yet another case of an unsecured online database, Morales added that “the information compromised seems to be noncritical to the function of the DOD, although very personal and private to the people compromised, so it may have been an external database without the same level of controls as internal secret information.”
Support our mission to keep content open and free by engaging with theCUBE community. Join theCUBE’s Alumni Trust Network, where technology leaders connect, share intelligence and create opportunities.
Founded by tech visionaries John Furrier and Dave Vellante, SiliconANGLE Media has built a dynamic ecosystem of industry-leading digital media brands that reach 15+ million elite tech professionals. Our new proprietary theCUBE AI Video Cloud is breaking ground in audience interaction, leveraging theCUBEai.com neural network to help technology companies make data-driven decisions and stay at the forefront of industry conversations.