 INFRA
INFRA
 INFRA
INFRA
 INFRA
INFRA
A new malware campaign dubbed “GreyEnergy” is targeting information systems tied to critical infrastructure.
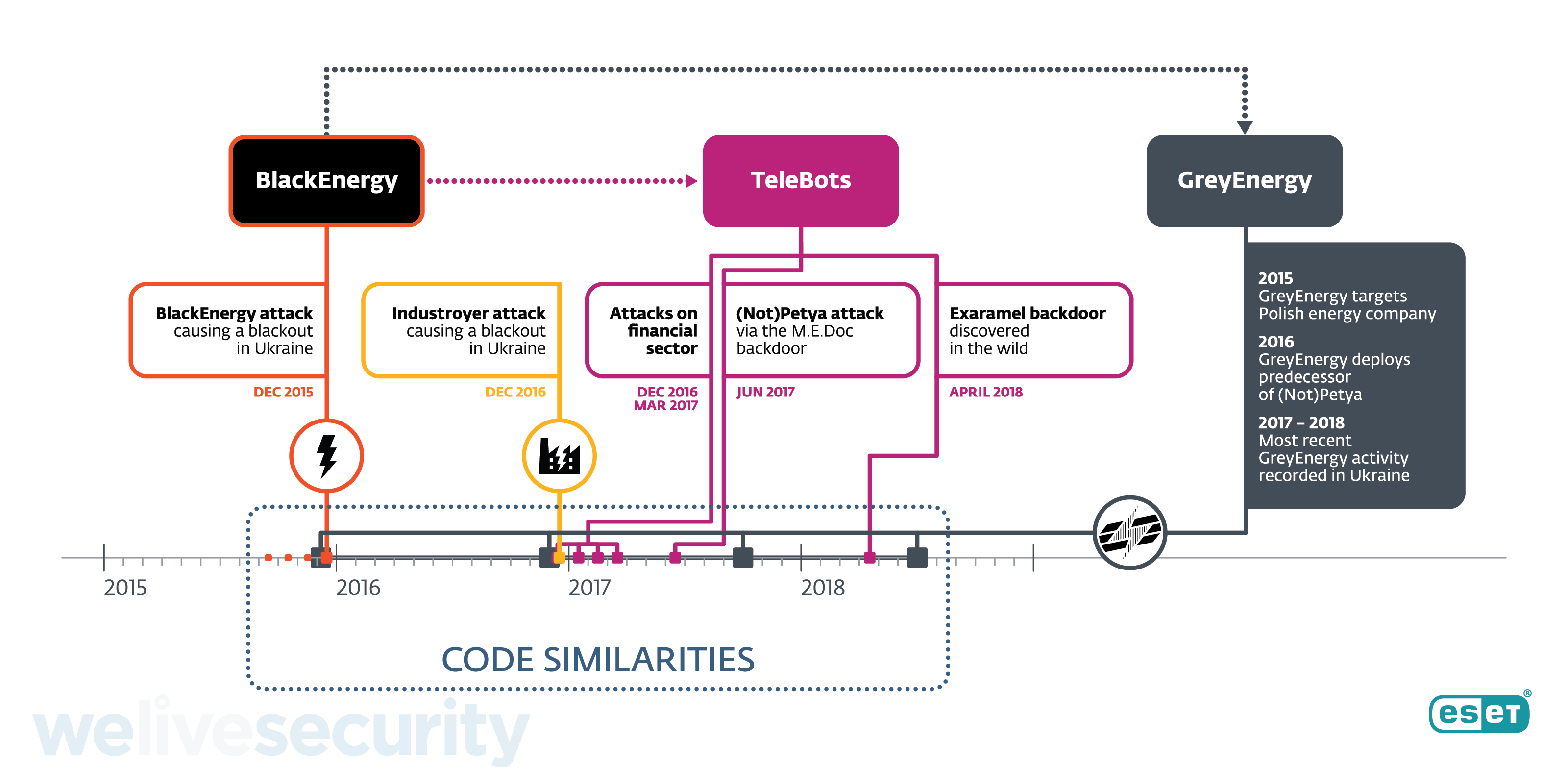
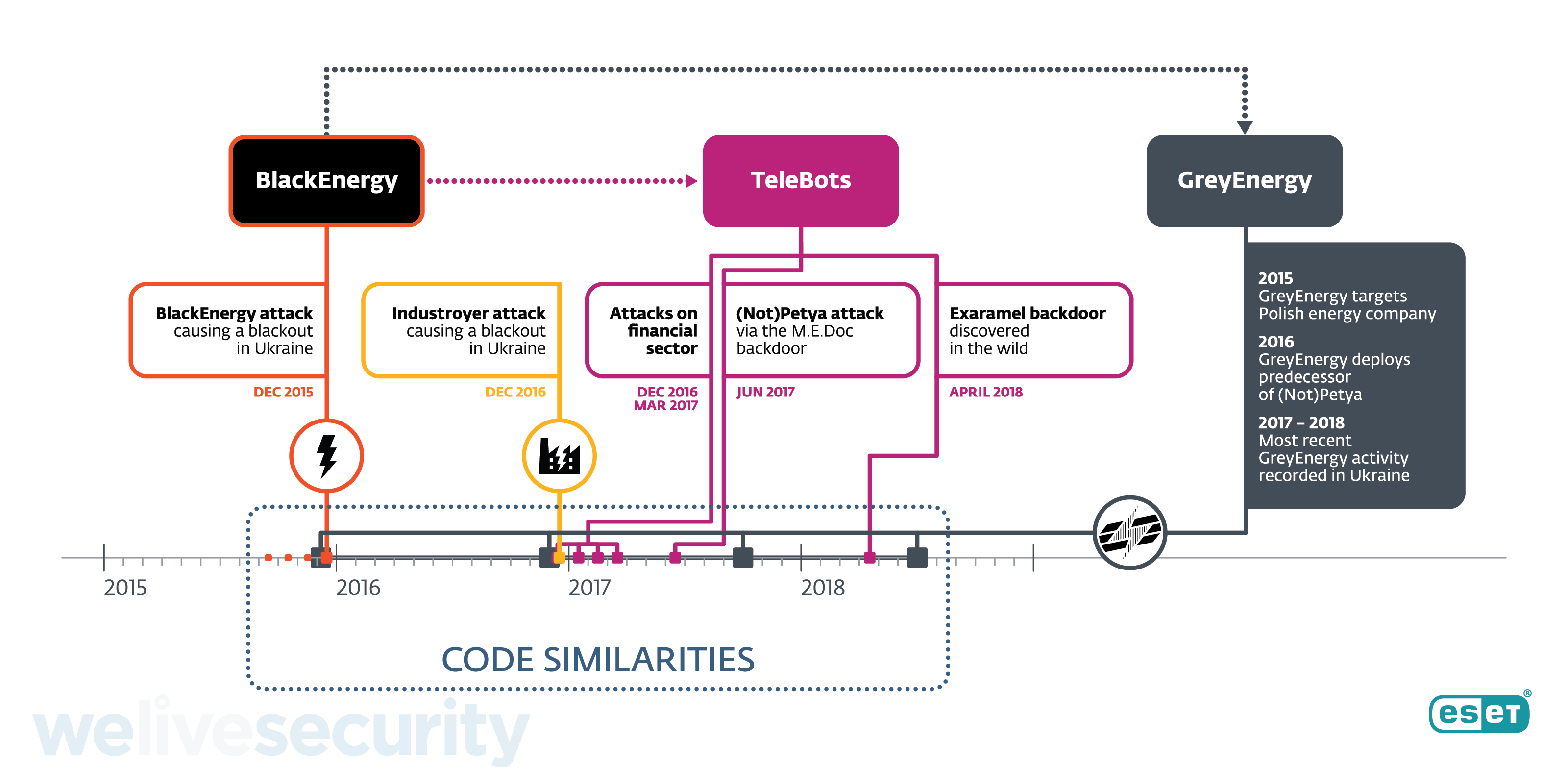
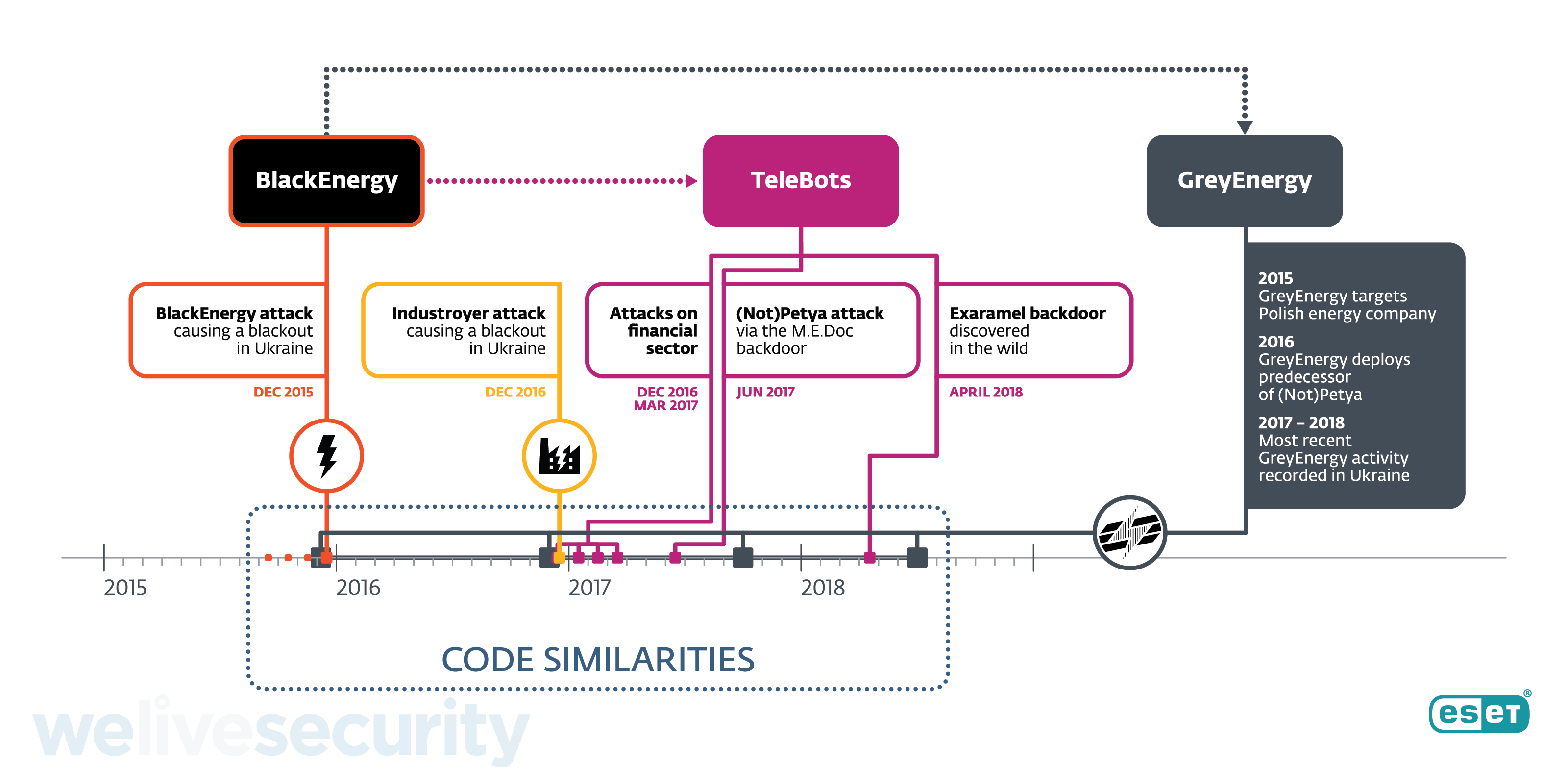
Discovered by researchers at ESET spol s.r.o. and reported Wednesday, the campaign is believed to be a successor to the BlackEnergy APT group. The attacks so far are targeting critical infrastructure and are described as a test in preparation for more damaging attacks.
BlackEnergy was a “trojan” virus that was used to conduct distributed denial-of-service attacks, cyberespionage and information destruction attacks back in 2014, primarily in Ukraine.
GreyEnergy is said to share a similar malware framework BlackEnergy and has been designed specifically to target industrial control systems. Like its predecessor, the primary target is again Ukraine, but it has also been detected on similar systems in Poland and other European countries. That means that should it be acted upon, the damage could be widespread.
The attack vector for the malware is currently via two campaigns: spear phishing, or the method of posing as legitimate acquaintances or authorities to fooling people into giving up information, and the targeting of public-facing web servers.
Bob Huber, chief security officer at Tenable Inc., told SiliconANGLE that the news about the GreyEnergy malware campaign is “certainly concerning” but not surprising.
“Will it be the global wake-up call that we’ve been looking for? Maybe,” Huber said. “Since the blackout in Ukraine in December 2015, and likely long before that, advanced adversaries have been stealthily targeting critical infrastructure around the world, learning more and more about the mission-critical systems as they go.”
Huber said each new event is a “canary in the coal mine,” not an isolated incident. “By and large, critical infrastructure owners, operators and stakeholders have made significant strides to secure their systems from outside threats,” he said. “However, additional resources are required to identify and reduce their attack surface.”
Ultimately, Huber added, such persistent threats underscore the importance of visibility across information and operational technology assets. “Blind spots are where advanced adversaries live,” he said. “Shining a light on those areas is key to stopping an attack in its tracks.”
Support our mission to keep content open and free by engaging with theCUBE community. Join theCUBE’s Alumni Trust Network, where technology leaders connect, share intelligence and create opportunities.
Founded by tech visionaries John Furrier and Dave Vellante, SiliconANGLE Media has built a dynamic ecosystem of industry-leading digital media brands that reach 15+ million elite tech professionals. Our new proprietary theCUBE AI Video Cloud is breaking ground in audience interaction, leveraging theCUBEai.com neural network to help technology companies make data-driven decisions and stay at the forefront of industry conversations.