Isha Suri
Latest from Isha Suri
Gauss Becomes the Next Big Topic in Nation-state Cyber Surveillance Realm
Accompanying Stuxnet, Flame, and Duqu, Gauss has become the latest cyber-surveillance operation in the entire cyber espionage scenario. Gauss is a nation state sponsored banking Trojan, and was discovered by International Telecommunications Union (ITU) that was working toward mitigating the risks posed by cyber-weapons. Gauss derives its name from one of its important modules, named ...
Apache Cassandra to Get Database Upgrade This October
When you need scalability and high availability without compromising performance, perhaps Apache Cassandra is the best choice. This open source NoSQL database got its 1.0 release stage last October, and will be getting the Version 1.2 in this October. Currently used by several big organizations, such as Disney, eBay, and Netflix, Cassandra 1.2 will have ...
White House Exploring Executive Order to Pass Cybersecurity Act
Following the proposal of Cybersecurity Act, White House is exploring an Executive Order nudge a bill designed to enable critical infrastructure owners implement better controls for protecting their computer networks. The bill in question is sponsored by Senators Joseph Lieberman (Ind,-CT) and Susan Collins, (R-ME) and several other democratic lawmakers. Soon, they will also prompt ...
Need for Security Monitoring Strengthens Across IT Industry
Security and cyberthreats, across entire IT industry, are intensifying like never before. Cyber attacks have not only shot up in numbers, but have also become stealthy, sophisticated, and damaging. What else is bothering security professionals? What do they feel necessary to combat this mess? Perhaps, better monitoring requisites. A recent ESG Research survey revealed some ...
1Password Gears Up for John the Ripper
1Password, a popular system and online security program has confirmed that it is now ready to tackle John the Ripper, but users need to have a good Master Password. The pre-eminent password cracking tool, John the Ripper, runs on fifteen different platforms, and can be run against various encrypted password formats including several crypt password ...
Stash 1.2 for Enterprise Git Released – What Does it Have to Offer?
As Git is becoming a basic need for developers across global enterprises, here comes a new version to cheer up the developers. Atlassian, the Sydney based company and the creator of business enterprise software targeted at software developers, has just released the Stash 1.2 version. The company launched the maiden version of the software two months back, and has ...
BMC Acquires VaraLogix, Enhances Fast Application Deployment
BMC Software today announced a strategic acquisition, where it acquired VaraLogix, a proven application release automation provider. Headquartered in Houston, Texas, BMC Software has a leading Business Service Management platform, Cloud Management, and the industry’s broadest choice of IT management solutions, and helps customers cut costs, reduce risk and achieve business objectives. Started in 1980, ...
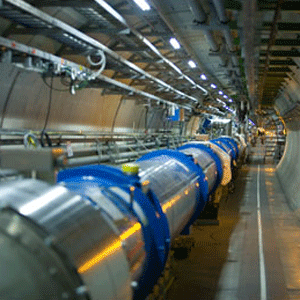
How we do Big Data to Compute for the Large Hadron Collider
We have seen Big Data utilized for several big computing applications, and it will now serve for computing for the Large Hadron Collider (LHC). It’s because the European Organisation for Nuclear Research (CERN) is facing a tough challenge in the discovery of a particle consistent with the Higgs Boson. CERN has to keep the Large ...
Microsoft Releases Attack Surface Analyzer 1.0 to Evaluate Malware Attacks
Microsoft recently released the Attack Surface Analyzer 1.0, whose beta version was launched last year. The tool is useful for software developers, especially during the verification phase of the Microsoft software lifecycle, and helps understand changes in Windows systems’ attack surface resulting from the installation of new application. As compared to the beta version, this ...
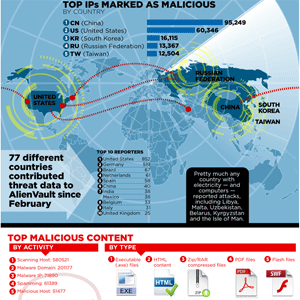
Global Cyberthreats intensify, China and U.S. Primary Source of Malicious IPs
AlienVault, the only open Unified Security Management platform that delivers built-in controls and full visibility, has released an infographic giving details of trends in malicious cyber activity. Named as “The 2nd United Nations”, the infographic gives out the latest threat data generated by the AlienVault Open Threat Exchange™ (OTX). Here are some key revelations from ...