Watch out pervs: Ransomware holds Android phones hostage
![]() Bad guys have cooked up the first strain of file-encrypting ransomware targeted at smartphones running Android.
Bad guys have cooked up the first strain of file-encrypting ransomware targeted at smartphones running Android.
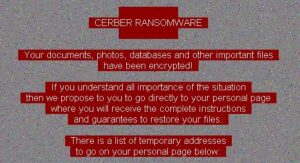
Called Android/Simplocker, the malware was spotted by the security firm ESET. Researchers say it works by scanning Android phone’s SD cards looking for certain types of files, before encrypting them and demanding payment to release the data.
The origins of this malware are a dead giveaway, as the ransom demand is written in Russian and payment is demanded in Ukrainian currency. The trick is similar to that of ransomware seen on PCs, with victims being accused of “viewing and distributing child pornography, zoophilia and other perversions”, says ESET. As a result, ‘law enforcement’ has locked-down the phone and demanded payment of a ‘fine’ as punishment for these misdemeanors.
The “unlock fee” is pretty cheap though, as the hackers demand a princely sum of just $16. That’s far less than the $300 demanded by notorious PC ransomware CryptoLocker. In the case of Android/Simplocker, payment has to be sent via the MoneXy eWallet service, which is notoriously difficult to trace.
ESET says the malware is pretty basic, and is likely just a proof-of-concept, which means the creators will probably come up with something nastier later on. However, ESET’s researchers admitted they don’t really understand how the malware spreads. A sample that they probed was discovered in an app called “Sex xionix”, which suggests Android/Simplocker is a Trojan that disguises itself as a legitimate app.
Android/Simplocker is more advanced than another nasty that made headlines recently, the fake security app called Virus Shield, which does absolutely nothing but cost money. It’s also pretty difficult to get rid of, as peg, jpg, png, bmp, gif, pdf, doc, docx, txt, avi, mkv, 3gp and mp4 files are all encrypted with AES. ESET suggests backing up your phone regularly so these files can be recovered.
More information on the threat, including screenshots, can be found at the WeLiveSecurity blog.
photo credit: CEBImagery.com via photopin cc
A message from John Furrier, co-founder of SiliconANGLE:
Your vote of support is important to us and it helps us keep the content FREE.
One click below supports our mission to provide free, deep, and relevant content.
Join our community on YouTube
Join the community that includes more than 15,000 #CubeAlumni experts, including Amazon.com CEO Andy Jassy, Dell Technologies founder and CEO Michael Dell, Intel CEO Pat Gelsinger, and many more luminaries and experts.
THANK YOU