 INFRA
INFRA
 INFRA
INFRA
 INFRA
INFRA
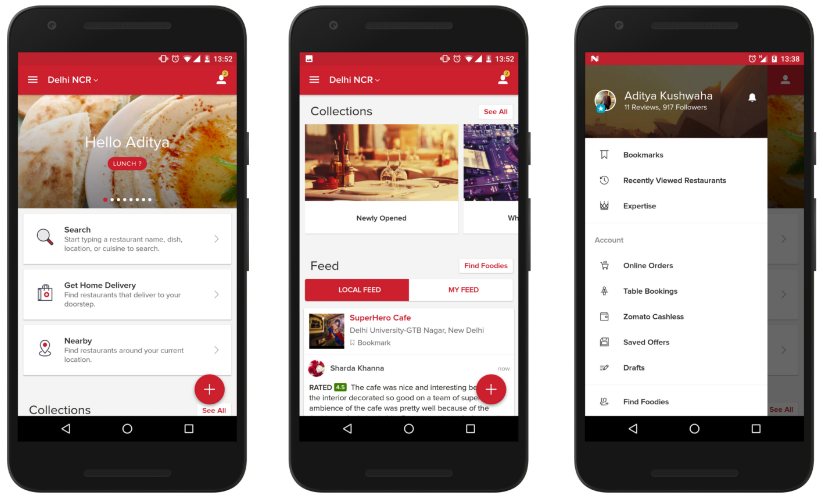
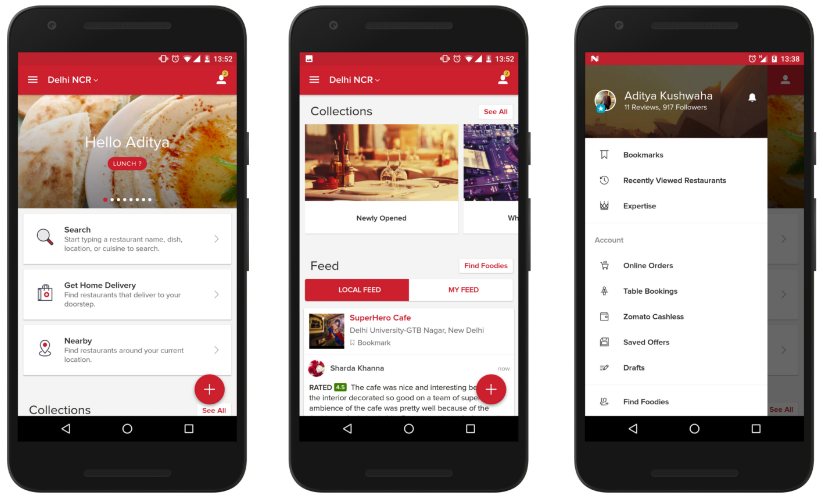
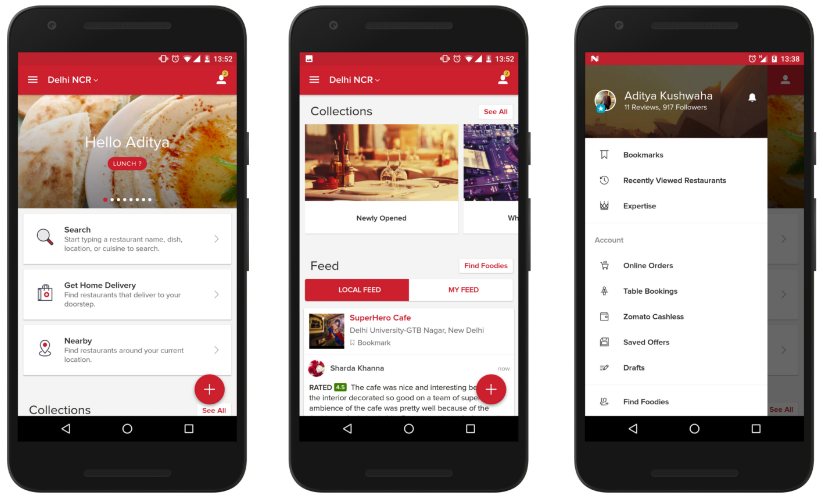
Food delivery and restaurant booking service Zomato Media Pvt Ltd. is the latest company to be hacked as the company disclosed early Thursday that the details of 17 million users worldwide have been compromised.
The company said in a blog post that hackers had obtained information such as user email addresses and passwords. It added that the passwords were encrypted, making it difficult for hackers to use them. Despite claiming that the passwords were safely hashed, Zomato nonetheless has reset passwords on all accounts affected by the hack and has advised users to change their passwords on any other online accounts that use the same email address and password combination.
“We hash passwords with a one-way hashing algorithm, with multiple hashing iterations and individual salt per password,” the company said. “This means your password cannot be easily converted back to plain text. We however, strongly advise you to change your password for any other services where you are using the same password.”
Although Zomato’s response is reasonable and to be expected by any company that has hacked, there is some question as to whether the passwords were actually encrypted in a secure manner. Motherboard claimed that copies of the hacked accounts that have appeared on the dark web use an outdated algorithm to encrypt customer passwords, making them easy to decrypt. The same report notes that Zomato was using MD5, a no longer widely used form of encryption that is known to have numerous vulnerabilities.
In a strange twist, Zomato now claims that it has been in contact with the person behind the hack. It said the unnamed individual, “very cooperative with us,” wanted Zomato to acknowledge security vulnerabilities with its system and to “work with the ethical hacker community to plug the gaps.”
The hacker also demanded that the company establish a bug bounty program. Zomato said it’s willing to implement one, so the hacker has agreed to remove listings for the hacked database from the dark web and to destroy copies of the data.
THANK YOU