 NEWS
NEWS
 NEWS
NEWS
 NEWS
NEWS
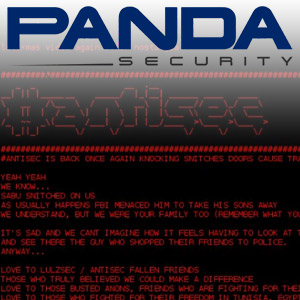
![]() Website defacement has become the mainstay of what essentially boils down to cybervandalism—and, just like its inner-city variant, it’s used as a medium to spread both playful and political messages. Yesterday, a multitude of subdomains belonging to security firm Panda Security were obliterated and replaced with cyber-graffiti scrawls, including a YouTube video, and the text-output of /etc/passwd and /etc/shadow files found on the machines.
Website defacement has become the mainstay of what essentially boils down to cybervandalism—and, just like its inner-city variant, it’s used as a medium to spread both playful and political messages. Yesterday, a multitude of subdomains belonging to security firm Panda Security were obliterated and replaced with cyber-graffiti scrawls, including a YouTube video, and the text-output of /etc/passwd and /etc/shadow files found on the machines.
This means that the usernames and passwords for the accounts on the machine compromised has been essentially aired in the public. Panda’s main site was not effected; but numerous subdomains were taken offline. Graham Cluley at Sophos’ Naked Security blog has an excellent takedown of the event.
The defacement is described by the attackers as payback for the recent arrests of five members of the now-defunct hacker group LulzSec:
hello friends!
pandasecurity.com, better known for its shitty ANTIVIRUS WE HAVE BACKDOORED, has earning money working with Law Enforcement to lurk and snitch on anonymous activists. they helped to jail 25 anonymous in different countries and they were actively participating in our IRC channels trying to dox many others. Aside how clueless they are and how disgusting they look sucking police tiny dicks and even how much fun we got when they are trying to sell IT security services xD that only helps to endanger people even more; they contribute to bring activist to jail. activists, not even hackers. common people who are trying desperately to denounce the injustices happening on their countries right now.
we should just say:
yep we know about you.
how does it feels being the spied one?
eat cock now.
The manifesto posted in crimson red on a black background cites a blog post by Panda Security’s Luis Corrons where he criticizes Anonymous for being “childish.” The blog post entitled “Where is the lulz now?” mentioned the arrests and calls out the hackers for their malicious activity—it is currently offline, but there’s a cached version available here.
Corrons has continued to discuss the attacks on his Twitter feed, @Luis_Corrons, and continues to call the AntiSec group out on the childishness of vandalizing a website: “Lads defending freedom of speech until they don’t like what you say #sadlulz”
Panda Security has used their Facebook page to make an official statement and makes it clear that the compromised server was used for PR campaigns and public facing activity; it was not part of Panda’s internal network, nor was it part of their security consulting activities. No customer data was accessed.
The attack did not breach Panda Security’s internal network and neither source code, update servers nor customer data was accessed. The only information accessed was related to marketing campaigns such as landing pages and some obsolete credentials, including supposed credentials for employees that have not been working at Panda for over five years.
As for the accusation made in the cyber-graffiti manifesto left by the AntiSec/Anonymous hackers, Panda Security says that they were not involved in the arrests of LulzSec members and did not consult with the FBI on the case.
Chances are they were targeted simply because the security on their PR webservers was lax and a small band of hackers from Anonymous managed to get through. By attacking their site and spreading the news that they’d been hacked, they can use that to springboard their message into the public eye.
This is what we can probably expect for much political revenge manifestos delivered from the hacker fringe of Anonymous: messages spray-painted across the storefront windows of the Internet calling out for attention.
Support our mission to keep content open and free by engaging with theCUBE community. Join theCUBE’s Alumni Trust Network, where technology leaders connect, share intelligence and create opportunities.
Founded by tech visionaries John Furrier and Dave Vellante, SiliconANGLE Media has built a dynamic ecosystem of industry-leading digital media brands that reach 15+ million elite tech professionals. Our new proprietary theCUBE AI Video Cloud is breaking ground in audience interaction, leveraging theCUBEai.com neural network to help technology companies make data-driven decisions and stay at the forefront of industry conversations.