 INFRA
INFRA
 INFRA
INFRA
 INFRA
INFRA
Hackers are reported to be targeting Oracle WebLogic server installations after a patch issued for a critical vulnerability earlier this month both disclosed the vulnerability and didn’t fix it properly.
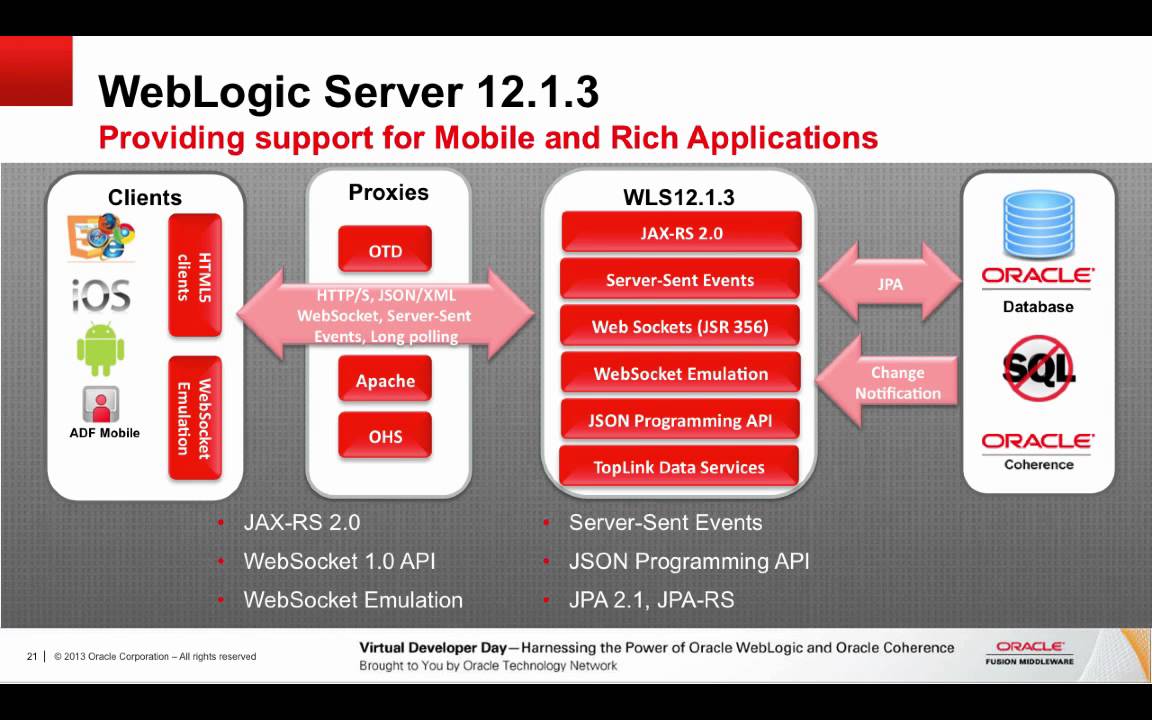
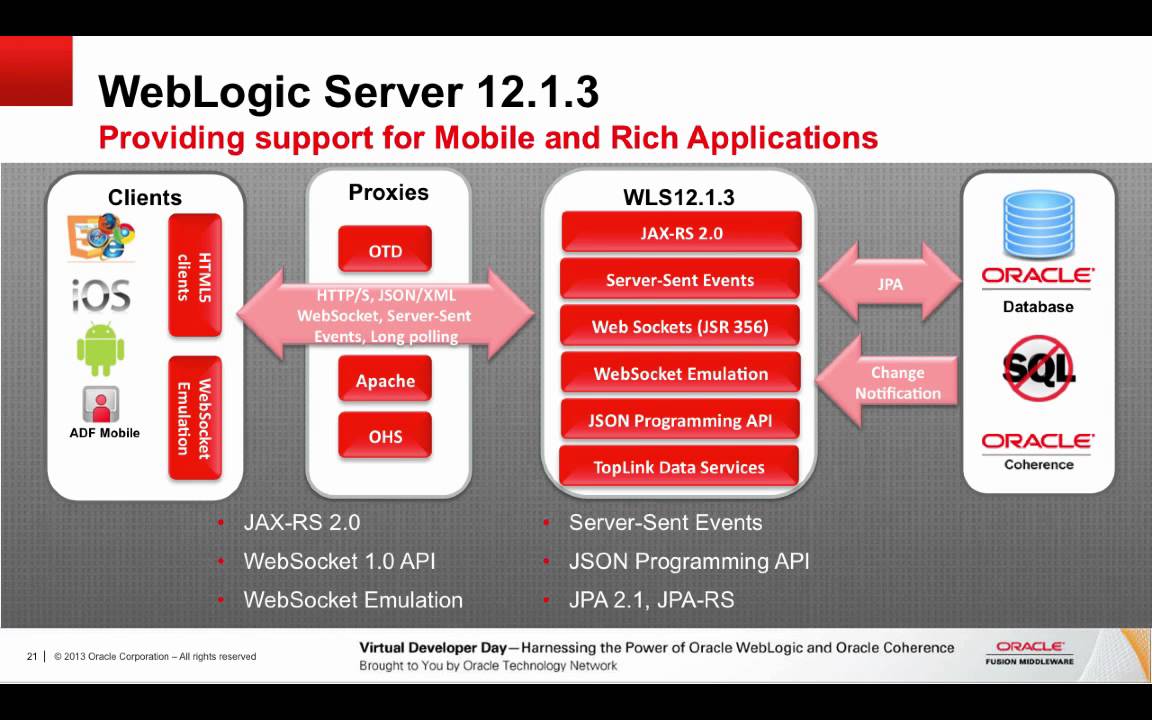
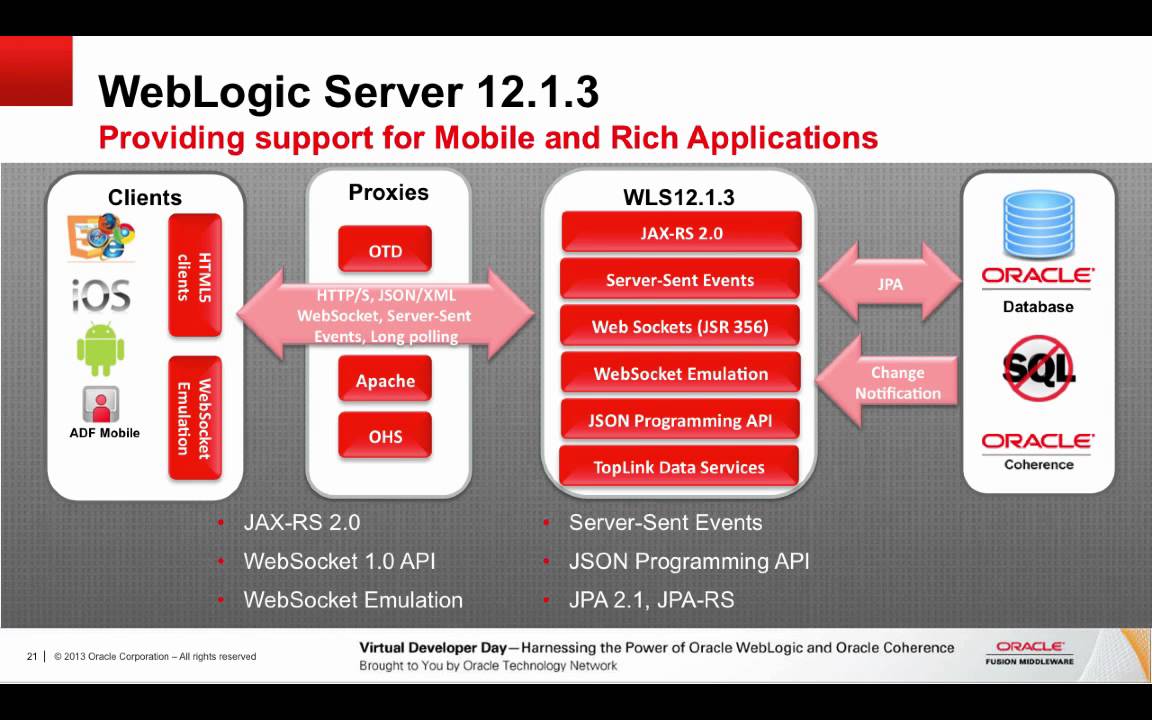
The story starts unremarkably, with Oracle offering a patch for the previously undisclosed critical vulnerability CVE-2018-2628 as part of its April patch release. The vulnerability is a critical remote command execution flaw affecting versions 10.3.6.0, 12.1.3.0, 12.2.1.2 and 12.2.1.3 of the Oracle WebLogic Server (Fusion Middleware) Java EE application server.
Oracle credited the discovery to Liao Xinxi of NSFOCUS Security Team, who detailed the patch vulnerability in a Chinese language blog post April 18. Bleeping Computer reported that a researcher by the name of Brianwrf subsequently released a proof-of-concept code on GitHub that could exploit the flaw.
Those two steps led to a surge in hackers scanning port 7001 on WebLogic installations, although there’s no confirmation at this time of any widespread hacking. Typically the revelation of a vulnerability does result in interest by hackers looking for unpatched installs.
But then the story takes an unexpected twist. As it turns out, security researchers are now claiming that the patch itself is “incomplete” and that it can be easily bypassed by attackers.
Researcher Kevin Beaumont was the first to raise the alarm. He wrote on Twitter that “there’s a zero-day [vulnerability] in Oracle WebLogic because the April patch didn’t fix the issue properly” and that “this is going to keep being an evergreen tweet. It looks like Oracle isn’t even fixing the issues here, they’re just blacklisting commands. In this case they missed the very next command.”
#CVE-2018-2628 Weblogic Server Deserialization Remote Command Execution. Unfortunately the Critical Patch Update of 2018.4 can be bypassed easily. pic.twitter.com/Vji19uv4zj
— pyn3rd (@pyn3rd) April 28, 2018
Another researcher, described as an Alibaba Cloud engineer, claimed that Oracle has botched the CVE-2018-2628 patch, since there is an easy way to bypass it and exploit the flaw even on supposedly patched WebLogic systems.
For those running Oracle WebLogic, the best advice, at least until such time Oracle releases a new patch, comes from Beaumont. He said — and this is for IT admins and others who can understand this — to “make sure port 7001 TCP is blocked inbound to your Fusion stack boxes.”
Support our mission to keep content open and free by engaging with theCUBE community. Join theCUBE’s Alumni Trust Network, where technology leaders connect, share intelligence and create opportunities.
Founded by tech visionaries John Furrier and Dave Vellante, SiliconANGLE Media has built a dynamic ecosystem of industry-leading digital media brands that reach 15+ million elite tech professionals. Our new proprietary theCUBE AI Video Cloud is breaking ground in audience interaction, leveraging theCUBEai.com neural network to help technology companies make data-driven decisions and stay at the forefront of industry conversations.