 SECURITY
SECURITY
 SECURITY
SECURITY
 SECURITY
SECURITY
A report from April that was published for the first time by the U.S. Department of Defense last week has found that cybersecurity at ballistic missile installations varied from lax to outright bad.
The report, first detailed by ZDNet today, said the DoD Inspector General audited five separate locations that are part of the Ballistic Missile Defense System program. That program is tasked with protecting U.S. territory through the interception of nuclear missiles.
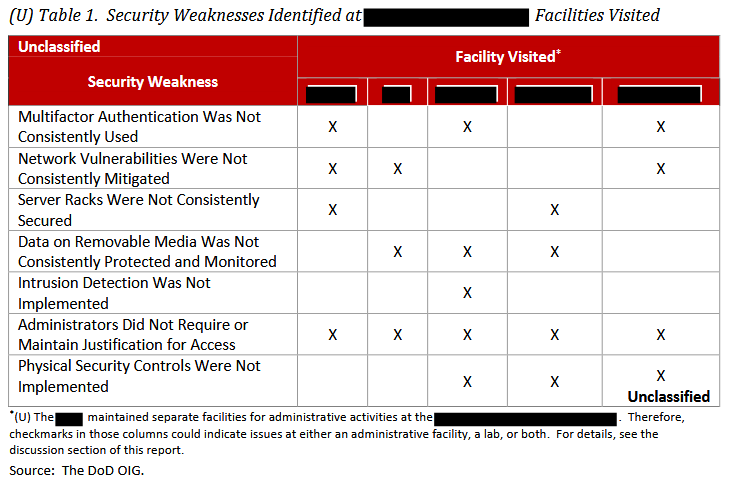
Every single location audited had security issues.
At three locations, two-factor authentication was only partially used or not used at all. Something as simple as patching vulnerabilities in software was also lacking at three locations, while physical security controls to servers were also not limited.
All five locations failed on maintaining justification for access, meaning they would not regularly purge older accounts from their networks.
The report covered five locations of a network of 104, but the report noted that if applied across all of them, the entire network could be easily attacked in the case of a conflict.
Not everyone was negative on the news. Lamar Bailey, director of security research and development at Tripwire Inc., told SiliconANGLE that although the report at first glance this sounds horrible, the key word in the findings is “consistently.” He noted that a table in the report (above) shows results for the facilities visited broken down into weaknesses in the seven areas audited.
“Only one audit hit all five locations and this dealt with justification for access,” Bailey explained. “Five of the weaknesses say they were not ‘consistently’ used but this can apply to ‘administrative, facility, a lab or both’ so they may not apply to the networks with the defense/offense controls.”
He also noted that the audit was only done at five facilities, fewer than 5 percent of those in operation. “We should not take a Chicken Little stance here, but remember basic security hygiene and foundational security controls apply to everyone,” he added.
Support our mission to keep content open and free by engaging with theCUBE community. Join theCUBE’s Alumni Trust Network, where technology leaders connect, share intelligence and create opportunities.
Founded by tech visionaries John Furrier and Dave Vellante, SiliconANGLE Media has built a dynamic ecosystem of industry-leading digital media brands that reach 15+ million elite tech professionals. Our new proprietary theCUBE AI Video Cloud is breaking ground in audience interaction, leveraging theCUBEai.com neural network to help technology companies make data-driven decisions and stay at the forefront of industry conversations.