 SECURITY
SECURITY
 SECURITY
SECURITY
 SECURITY
SECURITY
Security researchers have discovered a new form of adware buried in more than 200 hundred Android apps listed in the Google Play Store that may have infected in excess of 100 million users.
Detailed by researchers at Check Point Software Technologies Ltd., the “SimBad” malware was discovered on 206 applications that had been downloaded nearly 150 million times.
Traditional adware typically hijacks ads or displays additional ads to users, but SimBad is that and more, reflecting a far more serious malware threat.
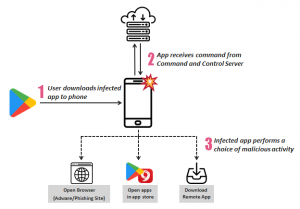
Along with displaying ads, SimBad allows the attacker to install applications remotely, opening certain URLs in the browser and open certain apps that can cause trouble, such as malware.
The ability to install applications remotely presents the biggest risk because it opens the door for the attack to install all sorts of malicious software, with SimBad acting as the gateway.
Some of the apps found to be infected include Snow Heavy Excavator Simulator, Real Tractor Farming Simulator, Heavy Mountain Bus Simulator 2018, Hummer taxi limo simulator, Excavator Wrecking Ball Demolition Simulator, and Sea Animals Truck Transport Simulator.
The apps were removed from the Google Play Store after the Check Point researchers informed Google of their findings.
 Kevin Stear, lead threat analyst at JASK Inc., told SiliconANGLE that campaigns like these are all too commonplace and blamed them on a lack of appropriate governance and review processes for Android apps.
Kevin Stear, lead threat analyst at JASK Inc., told SiliconANGLE that campaigns like these are all too commonplace and blamed them on a lack of appropriate governance and review processes for Android apps.
“For these types of adware campaigns, it’s definitely possible for bad actors to evolve them into something more damaging – access is access,” Stear explained. “If a developer, or another third-party, can slide malicious code into an Android app, then it’s incredibly difficult to control how that access is being utilized by whom and for what purpose.”
For that reason, he added, “consumers should adopt basic cautionary practices to beef up their mobile security hygiene, such as knowing who develops the apps they download, being generally aware of the privileges apps have by actually reading EULAs and running some form of mobile security software to confirm things are behaving appropriately.”
Boris Cipot, senior security engineer at Synopsys Inc,. also advised users not to download any unknown apps or apps from unknown providers, at least not immediately.
“First of all, you need to at least try to see if the apps have real usage, if the apps have been rated and if the provider of the apps is trustworthy,” Cipot said. “On the other hand, all those things can be false data which the cybercriminals have made with fake users bought from the dark web.”
Cipot recommended users install anti-malware software since it provides “the opportunity of viewing the rating of the apps and checking if the installed app has any weird behavior listed or uses functionality that should not be there.”
Support our mission to keep content open and free by engaging with theCUBE community. Join theCUBE’s Alumni Trust Network, where technology leaders connect, share intelligence and create opportunities.
Founded by tech visionaries John Furrier and Dave Vellante, SiliconANGLE Media has built a dynamic ecosystem of industry-leading digital media brands that reach 15+ million elite tech professionals. Our new proprietary theCUBE AI Video Cloud is breaking ground in audience interaction, leveraging theCUBEai.com neural network to help technology companies make data-driven decisions and stay at the forefront of industry conversations.