 SECURITY
SECURITY
 SECURITY
SECURITY
 SECURITY
SECURITY
Details of more the 2.28 million users of dating site MeetMindful have been released online for free in the latest in a series of stolen data dumps.
The stolen data includes real names, email addresses, address information, body details, dating preferences, marital status, birth data, location data, IP addresses, Bcrypt-hashed passwords, Facebook user IDs and Facebook authentication tokens. The inclusion of Facebook authentication tokens is particularly notable because it could potentially give access to the Facebook accounts of MeetMindful members in the database.
MeetMindful has not publicly addressed either the theft of its user data or its publication online.
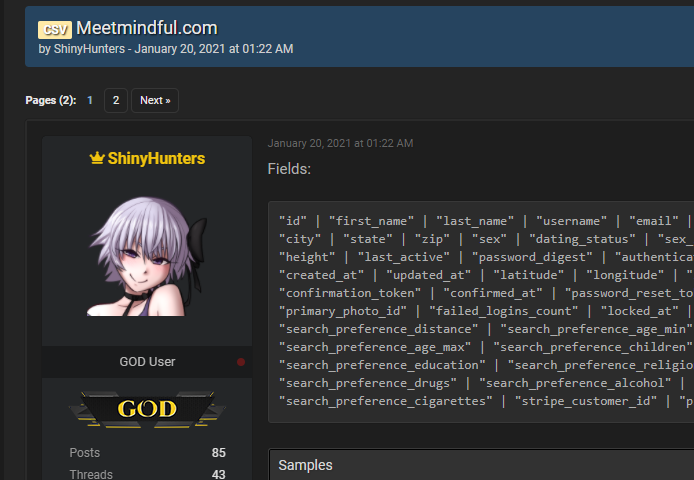
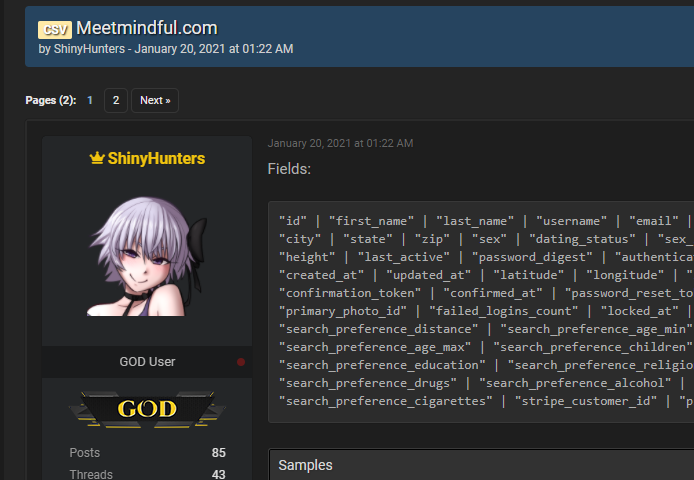
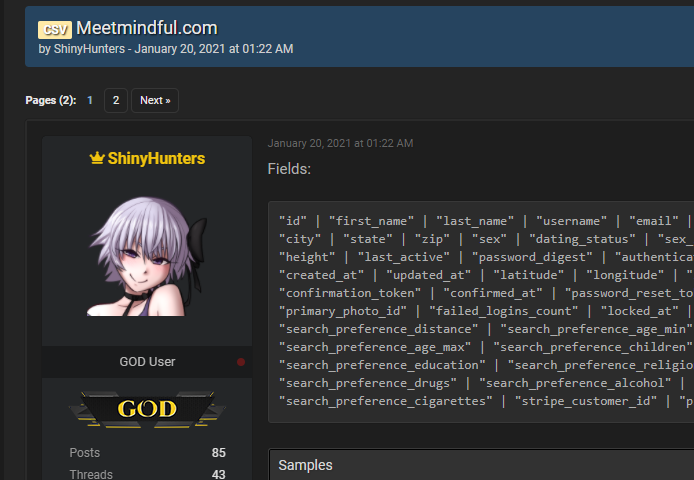
ZDNet first reported the news today, saying only that the data was released by a “well-known hacker” as “a free download on a publicly accessible hacking forum known for its trade in hacked databases.” SiliconANGLE can confirm the data in question was released by ShinyHunters Jan. 20 and the forum was Raid Forums, a popular internet forum used by hackers which is easily found via Google search.
ShinyHunters has been rather busy lately. It was reported last week that it had published 1.9 million stolen user records from the free online photo editing service Pixlr as part of a release of hacked data from various sites. Researchers at cybersecurity intelligence firm Kela Research and Strategy Ltd. also discovered stolen data released on Raid Forums from Wongnai Media Co. Ltd., Tuned Global Pty. Ltd., Buyucoin, Wappalyzer, Teespring Inc. and Bonobos.com.
It’s not known how the data was stolen from MeetMindful, but ShinyHunters is particularly fond of obtaining data from misconfigured Amazon Web Services Inc. databases and S3 buckets.
“Improperly secured AWS S3 buckets are one of the leading causes of data breaches due to misconfiguration,” Pravin Rasiah, vice president of product at cloud management platform company CloudSphere, told SiliconANGLE. “The chances of leaving an S3 bucket exposed are all too high, as inexperienced users can simply choose the ‘all users’ access option, making the bucket publicly accessible. Leaving these S3 buckets open and exposed invites hackers to exploit the personal data entrusted to companies by their customers.”
To prevent incidents like this from occurring, Rasiah added, “awareness within the cloud environment is imperative. Businesses should invest in a cloud governance platform that provides holistic, real-time observability into the cloud landscape to stay apprised of abnormalities while ensuring that data is secure.”
Support our mission to keep content open and free by engaging with theCUBE community. Join theCUBE’s Alumni Trust Network, where technology leaders connect, share intelligence and create opportunities.
Founded by tech visionaries John Furrier and Dave Vellante, SiliconANGLE Media has built a dynamic ecosystem of industry-leading digital media brands that reach 15+ million elite tech professionals. Our new proprietary theCUBE AI Video Cloud is breaking ground in audience interaction, leveraging theCUBEai.com neural network to help technology companies make data-driven decisions and stay at the forefront of industry conversations.