 INFRA
INFRA
 INFRA
INFRA
 INFRA
INFRA
A vulnerability in Nvidia Corp.’s Tegra X-1 chips used by the Nintendo Switch, Google LLC’s Pixel C tablet and the Nvidia Shield digital media box that allows the devices to be easily hacked has been uncovered by a security researcher, but the worst part is that it may not be patchable.
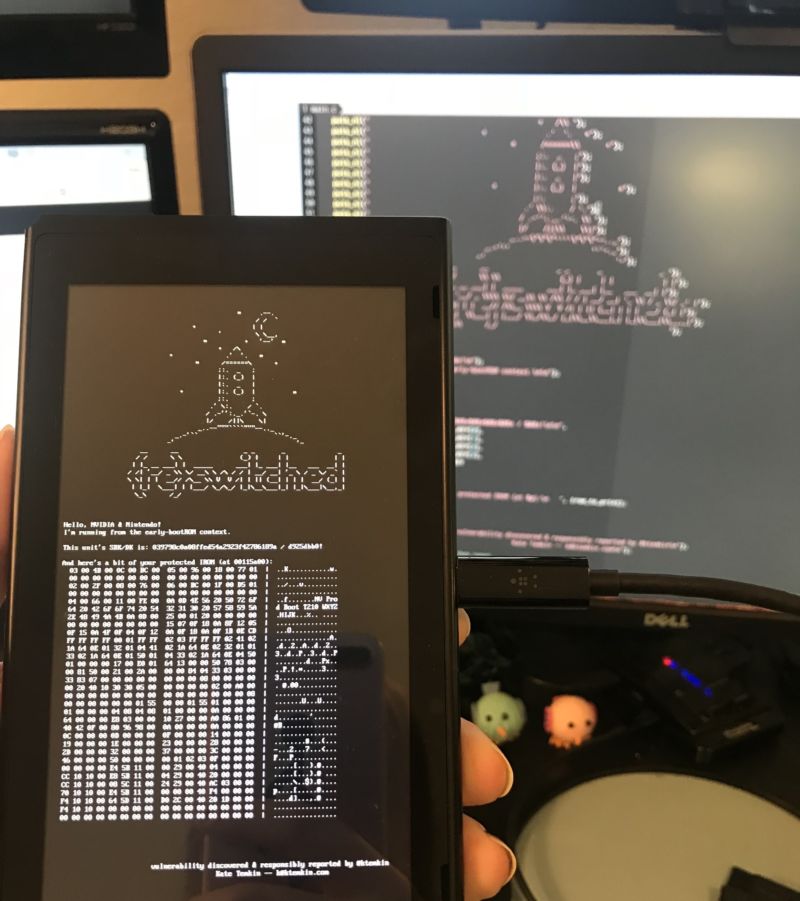
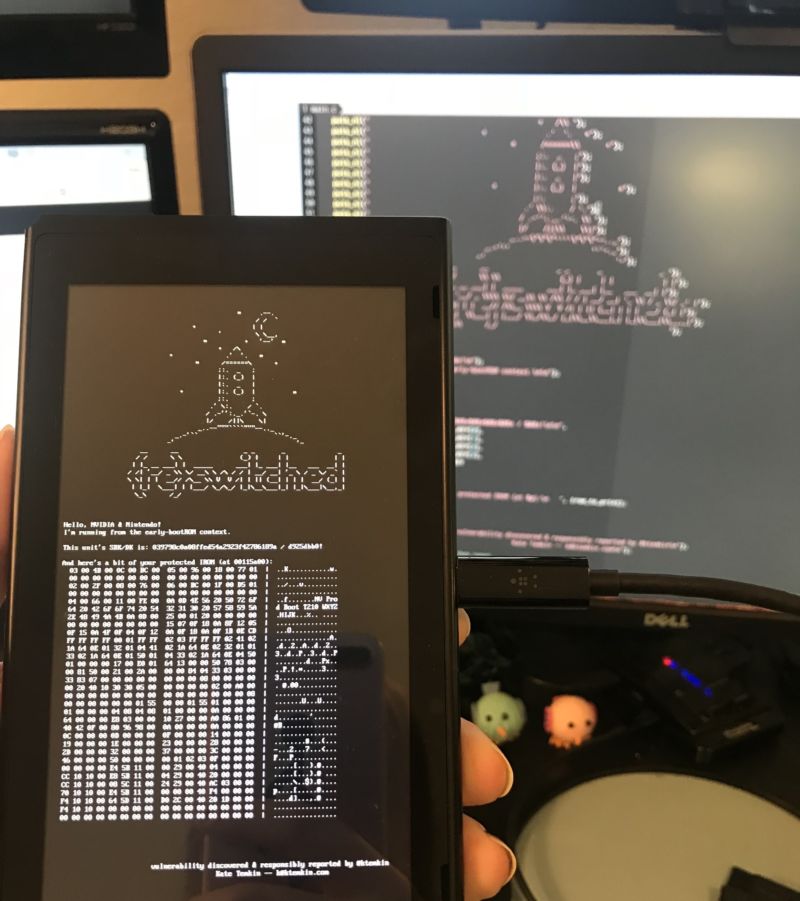
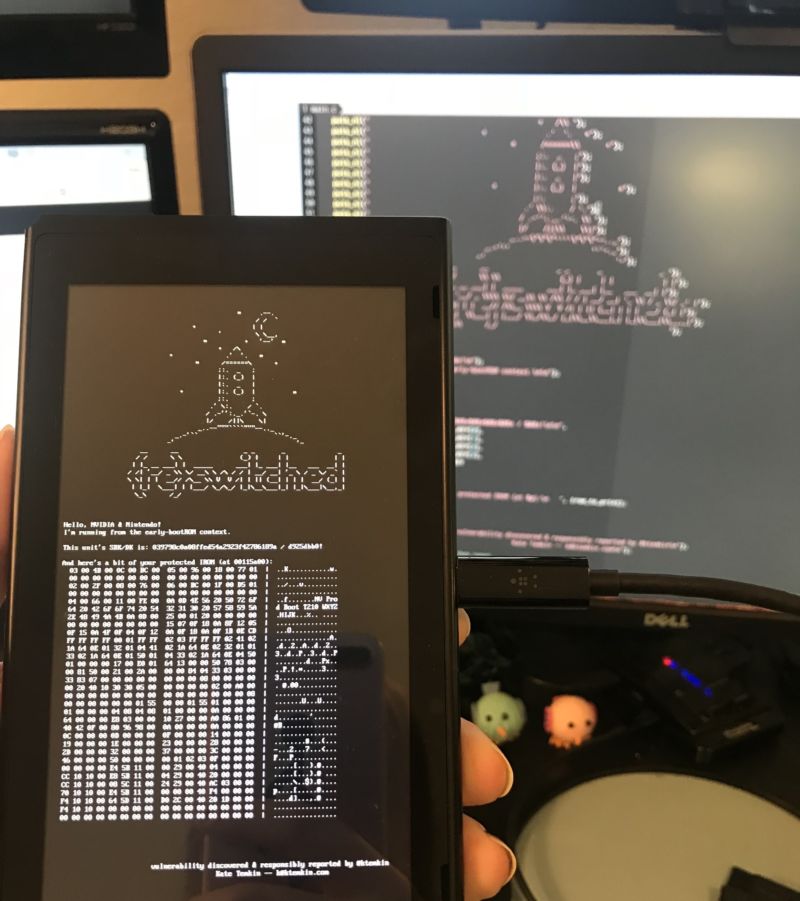
A proof-of-concept attack exploiting the vulnerability, dubbed Fusée Gelée by researcher Katherine Temkin, allows an attacker to bypass the device lockdown and run custom code on the Nintendo Switch specifically. But in theory, it could be used on any device with a Tegra X-1 chip.
The hack involves exploiting the chip’s USB recovery mode to circumvent the lock-out operations that protect the bootROM, which is the first code executed by the processor when a device is turned on or reset. A buffer overflow, essentially a bunch of bad data, is sent through the USB control procedure, overflowing the direct memory access buffer in the bootROM, allowing data to be copied to the previously protected application stack.
In the proof of concept, Temkin installed Linux on a Nintendo Switch, but given that the access opens the door to hacking, anything could be installed, including malicious software.
Although a vulnerability alone may be bad, what’s worse is that Temkin says that it’s unpatchable because it’s built into the hardware. “The relevant vulnerability is the result of a ‘coding mistake’ in the read-only bootROM found in most Tegra devices,” Temkin explained in a FAQ. “This bootROM can have minor patches made to it in the factory (‘ipatches’), but cannot be patched once a device has left the factory.”
Nintendo is yet to officially comment on the disclosure, but there may be at least some hope for the company. Ars Technica noted that previous software-level exploits of Nintendo systems could be mitigated via downloadable system updates, which Nintendo attempts to force on users by making them a requirement for new software and access to Nintendo’s online servers. Although adding that such an application isn’t helpful for a chip-level bootROM exploit, Nintendo may still be able to detect hacked systems via a software update, allowing it to restrict access to machines that have been hacked.
Support our mission to keep content open and free by engaging with theCUBE community. Join theCUBE’s Alumni Trust Network, where technology leaders connect, share intelligence and create opportunities.
Founded by tech visionaries John Furrier and Dave Vellante, SiliconANGLE Media has built a dynamic ecosystem of industry-leading digital media brands that reach 15+ million elite tech professionals. Our new proprietary theCUBE AI Video Cloud is breaking ground in audience interaction, leveraging theCUBEai.com neural network to help technology companies make data-driven decisions and stay at the forefront of industry conversations.