Duncan Riley
Latest from Duncan Riley
Hotspot Shield VPN software accused of spying on users and injecting ads
Popular virtual private network provider Hotspot Shield has been accused of spying on its users and injecting its own advertising into web pages, according to a newly filed Federal Trade Commission complaint. The accusations come from the Center for Democracy & Technology, which claims in its 14-page filing that Hotspot Shield is monitoring its users in breach ...
British model allegedly kidnapped for sale on the darknet
A British model is alleged to have been kidnapped and offered for sale on the darknet by the “Black Death Group,” a shadow organization that facilitates human trafficking. Twenty-year-old Chloe Ayling claims to have been lured for a modeling shoot to Milan, Italy, where she was then kidnapped on July 11 and taken to a ...
Bitcoin hits new record high as Bitcoin Cash alternative flounders
The price of a single bitcoin broke through $3,000 over the weekend, surging as initial interest in an alternative version of bitcoin launched last week declined. The price of bitcoin peaked at $3,323.93 in trading Saturday before dropping to $3,248.35 Sunday evening, according to figures from Coindesk. Along with the record price, bitcoin’s market capitalization also ...
U.S. Army bans use of Chinese-made DJI drones on cybersecurity risks
The U.S. Army has issued a blanket ban on all drones manufactured by Dà-Jiāng Innovations Science and Technology Co. Ltd., better known as DJI, over “cyber vulnerabilities” relating to the Chinese drone maker. First published Friday by drone industry site SAUS News, the Army memo, issued Aug. 2, stated that “due to increased awareness of cyber vulnerabilities ...
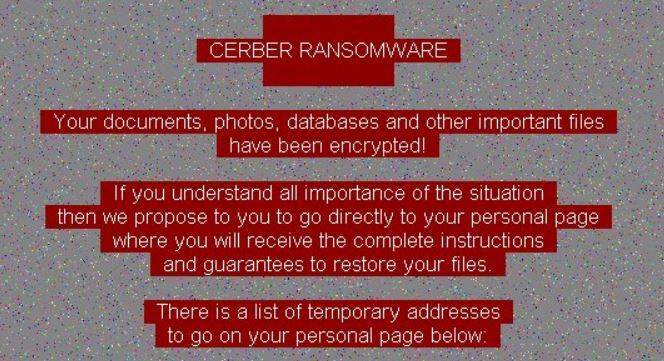
New version of Cerber ransomware targets bitcoin wallets
A new version of the infamous Cerber ransomware now steals bitcoin from wallets, according to newly published research. Gilbert Sison and Janus Agcaoili from Trend Micro Inc. detail the new version in a blog post, explaining that the new version of Cerber, which has gone through six separate versions with various differences in its routines, targets ...
Startup incubator Science looks to raise $50-100M in initial coin offering for new fund
Startup incubator Science Inc. is delving into the world of initial coin offerings with an ICO that will raise money for a new blockchain-focused investment fund. The Science Blockchain Fund, believed to be looking to raise between $50 million and $100 million according to The Wall Street Journal, intends to use the funds to invest in companies ...
Google Play Store will now rank apps based on performance and quality
Android users will be presented better-performing apps in the Google Play Store as the search giant announced that it has started ranking apps in search results. Now, “quality apps,” those that rate highly on “performance and quality expectations,” now appear above apps that have excessive battery usage, slow rendering times and crashes. According to Google Play Product Manager Andrew Ahn, ...
Researcher who stopped WannaCry arrested for involvement with banking virus
In a surprising twist to what was until now a positive story, the security researcher who stopped the WannaCry ransomware attack earlier this year has been arrested for his involvement with a banking “trojan” virus. British national Marcus Hutchins (pictured), 23, was arrested at the Las Vegas airport on Wednesday by U.S. Marshals on an ...
Security vulnerabilities in Amazon’s Echo can turn it into a spying device
Jokes about the Amazon Echo and similar smart home devices being self-installed wiretaps that monitor your every move have abounded since the devices were first launched. It turns out such jokes are now a reality, as a security researcher discovered that turning an Echo into a spying device is actually fairly easy to do. Mark Barnes from MWR ...
Researchers find security vulnerabilities in modems used by luxury cars
Researchers at security firm McAfee LLC have discovered two serious vulnerabilities in the telematics control unit used in a range of luxury cars that could potentially allow hackers to gain control of vehicles. A TCU is an embedded system that controls tracking of the vehicle, and in this case involves a unit manufactured by Continental AG that operates as a ...