Guest Author
Latest from Guest Author
Recession-proof? Forrester sees continued strong growth in enterprise software
Venture capitalist Marc Andreessen’s oft-quoted prediction that “software is eating the world” is borne out by Forrester Research Inc.’s latest global software industry forecast. Inflationary pressures, higher interest rates and geopolitical turmoil are expected to have little impact on a market for infrastructure and application software that should exceed $400 billion by 2023. That reflects ...
GUEST COLUMN
Cybersecurity innovation on full display at Black Hat
Cybersecurity professionals packed the Mandalay Bay Convention Center in Las Vegas this past week for the annual Black Hat USA confab, largely discarding their masks as they thronged into pre-COVID-style crowds. Security vendors large and small plied their wares, giving enterprise security professionals plenty of products to add to their cyber shopping list. Although many ...
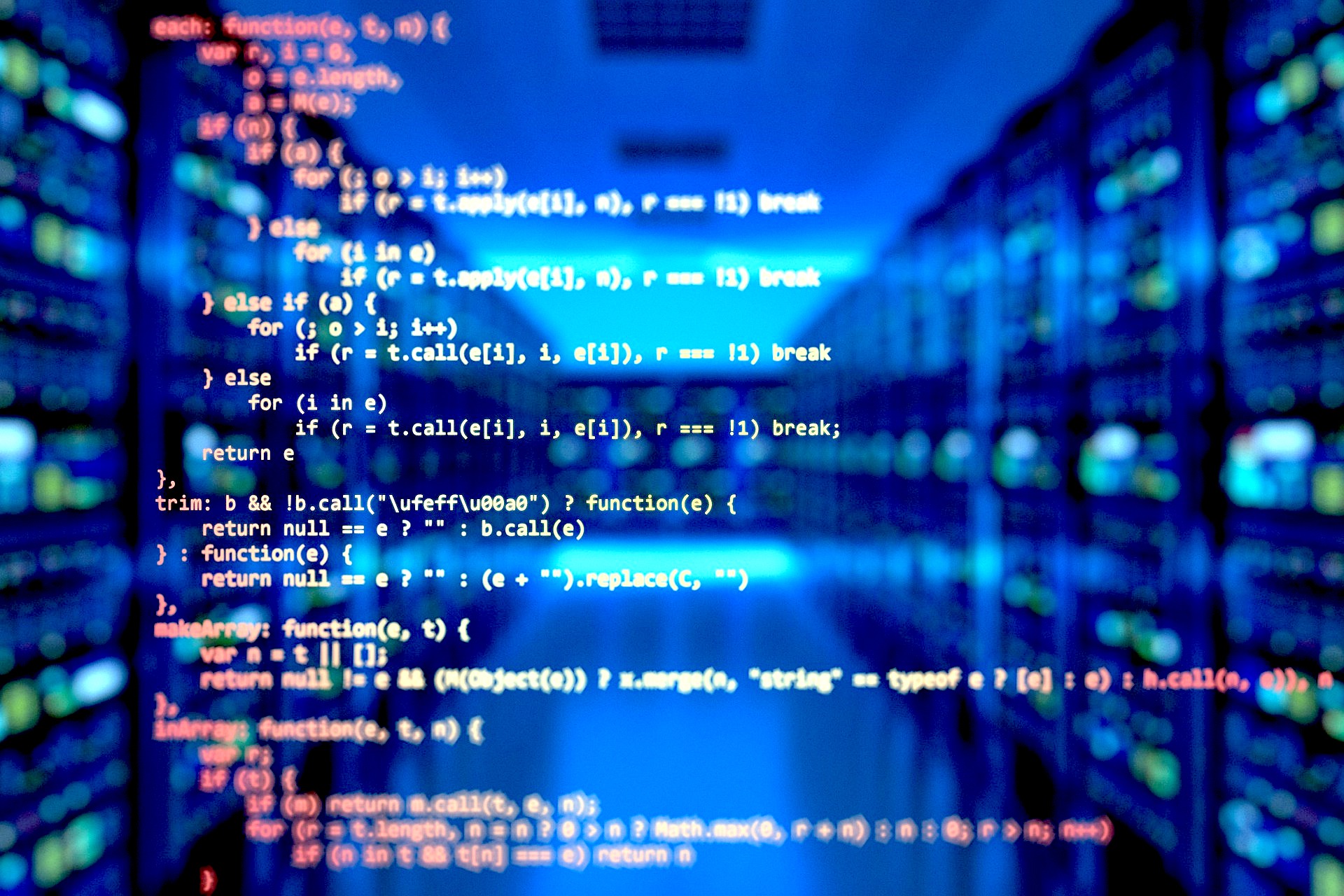
SPECIAL REPORT: SUPERCLOUD RISING
How industry cloud platforms will transform the next decade of cloud services
Hyperscale cloud providers are increasingly making headlines with the launch of new “industry cloud” platforms. Industry clouds platforms create value for enterprises by bringing together traditionally separately purchased cloud services in a pre-integrated, but adaptable way. Industry clouds offer not just technical but also business capabilities that are specifically relevant to identified vertical industries. Leaders ...
GUEST COLUMN
How IT leaders can make AI environmentally sustainable
Sustainable business is a strategy that incorporates environmental, social and governance factors into decision-making, and it is becoming an increasingly important component of business strategy. In fact, in a recent Gartner survey, chief executives identified environmental sustainability as a top 10 business priority for the first time in a decade. Technology is an essential part ...
GUEST COLUMN
Beyond the edge: Why SASE means improved security for your entire network
The rapid shift to hybrid work has transformed where and how work happens. Today’s workers are more likely to hop online from their home office than from the company’s main office, creating new challenges for the information technology security teams charged with keeping networks safe — and moving the edge to front and center. Amid ...
GUEST COLUMN
How FinOps can optimize cloud costs and drive innovation
Two mainstays drive most application migration and modernization initiatives. First, organizations are moving workloads to the cloud as an innovation catalyst. Achieving their strategic goals requires the speed, agility, reliability and advanced technical capabilities available to them in a hyperscale cloud. Second, they’re intent on ensuring the return on investment through cost optimization, which is ...
GUEST COLUMN
Three ways to patch your thinking about open-source software security
What comes to mind when you hear “open source?” Is it a community? Better-quality software? A technology advantage that helps companies scale quickly? If so, congratulations. You understand the value developing with open-source software can bring to a business — despite a lot of noise to the contrary. Recent headlines about OSS vulnerabilities paint open-source tools ...
GUEST COLUMN
Increasing cloud complexity is causing a seismic shift in the economics of IT
In the last year and a half, information technology departments have been critical to companies’ ability to amend their operational models and enable employees to work remotely. The responsibility for enabling their companies to navigate this transition — and prepare for an uncertain future — has given IT departments a considerable boost in strategic significance across ...
Cyber alert: The 10 numbers that might ruin your life
In perhaps one of the most audacious advertising campaigns in the history of personal security technology, LifeLock Inc. Chief Executive Todd Davis famously gave out his Social Security number in commercials that seemed to run on a loop on broadcast and cable television throughout the mid-2000s. Davis even went so far as to put the ...
GUEST COLUMN
How to manage artificial intelligence risk and security: Focus on five priorities
In most organizations, artificial intelligence models are “black boxes,” where only data scientists understand what exactly AI does. That can create significant risk for organizations. Large, sensitive datasets are often used to train AI models, creating privacy and data breach risks. The use of AI increases an organization’s threat vectors and broadens its attack surface. ...