 NEWS
NEWS
 NEWS
NEWS
 NEWS
NEWS
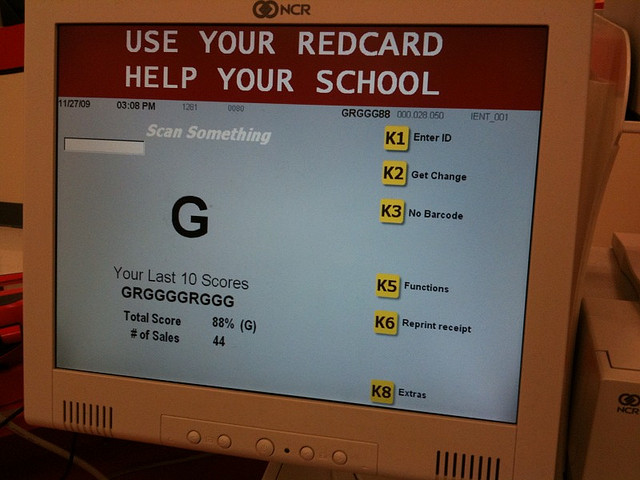
![]() Hardly a day went by since we heard that the big Target hack of December 2013 actually affected as many as 110 million people and that upscale retailer Neiman Marcus was also hacked that the cybercrime news has gotten even more interesting. According to a report from Reuters, three additional major retailers have also been hacked during the holiday shopping season. The names of the merchants have not been disclosed thus far, but they are reported to be smaller breaches at well-known U.S. retailers. The techniques used in these latest attacks are reportedly similar to the Target attack. Early yesterday the question was posed as to whether the Neiman Marcus and Target attacks were linked. The Reuters report lends more credence to that linkage, as their law enforcement sources strongly suspect the same perpetrators that appear to be originating from Eastern Europe were behind the attacks.
Hardly a day went by since we heard that the big Target hack of December 2013 actually affected as many as 110 million people and that upscale retailer Neiman Marcus was also hacked that the cybercrime news has gotten even more interesting. According to a report from Reuters, three additional major retailers have also been hacked during the holiday shopping season. The names of the merchants have not been disclosed thus far, but they are reported to be smaller breaches at well-known U.S. retailers. The techniques used in these latest attacks are reportedly similar to the Target attack. Early yesterday the question was posed as to whether the Neiman Marcus and Target attacks were linked. The Reuters report lends more credence to that linkage, as their law enforcement sources strongly suspect the same perpetrators that appear to be originating from Eastern Europe were behind the attacks.
In addition, the report indicates that investigators are pursuing the technique of ‘scraping memory’ – an attack that is indeed tied to malware as was first posited in our initial report of the breach:
Target has not disclosed how the attackers managed to breach its network or siphon off some of its most sensitive data.
The sources who spoke to Reuters about the breaches said that investigators believe the attackers used similar techniques and pieces of malicious software to steal data from Target and other retailers.
One of the pieces of malware they used was something known as a RAM scraper, or memory-parsing software, which enables cyber criminals to grab encrypted data by capturing it when it travels through the live memory of a computer, where it appears in plain text, the sources said.
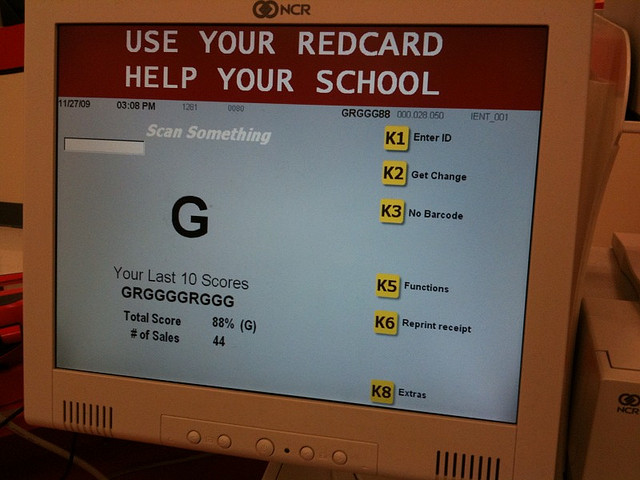
![]() In fact, as the report indicates, Visa put out two alerts to the retail industry with specific warnings about this type of malware attack. Visa’s knowledge of these types of attacks, which included technical details and prevention advice, indicates that Visa probably had some experience with this type of attack somewhere in the field. Though not a new type of attack, it is not unnatural to think that on this scale, the hackers behind this operation conducted one or a number of dry runs on other retailers and thus captured the attention of Visa. Apparently, even the advice that Visa did put out there may not have been able to stop the attack:
In fact, as the report indicates, Visa put out two alerts to the retail industry with specific warnings about this type of malware attack. Visa’s knowledge of these types of attacks, which included technical details and prevention advice, indicates that Visa probably had some experience with this type of attack somewhere in the field. Though not a new type of attack, it is not unnatural to think that on this scale, the hackers behind this operation conducted one or a number of dry runs on other retailers and thus captured the attention of Visa. Apparently, even the advice that Visa did put out there may not have been able to stop the attack:
“the attackers were more sophisticated than the ones in the previous attacks described in the Visa alerts, according to the source. The source asked not to be identified because they were not authorized to discuss the matter publicly.”
Let’s go with the obvious here – If indeed all these attacks can be strung together, it could end up being the biggest cumulative cybercrime incident in history, rivaling the 2008 Heartland Payment Systems breach that exposed 130 million U.S. debit and credit cards. At the very least, the coordination across various retailers tells us that something has gone horribly wrong. It could be a backdoor, it could be some common piece of compromised or non-hardened hardware, it could be something in the process. If indeed this turns out to be malware, it is especially horrifying to think that this got into the systems of at least five well-known retailers – that we know of. The Reuters report also says that earlier hacks may have happened earlier in the year. It’s not clear if those were at the same retailers, on U.S. soil. Again, this is a BIG story and more information can be expected. In the meantime, use cash if you can.
UPDATE – On Sunday evening, Target’s CEO Gregg Steinhafel confirms it was malware behind the breach.
“Sunday (Dec. 15) was really day one. That was the day we confirmed we had an issue and so our number one priority was … making our environment safe and secure. By six o’clock at night, our environment was safe and secure. We eliminated the malware in the access point, we were very confident that coming into Monday guests could come to Target and shop with confidence and no risk,” Steinhafel said.
“Day two was really about initiating the investigation work and the forensic work … that has been ongoing. Day three was about preparation. We wanted to make sure our stores and our call centers could be as prepared as possible, and day four was about notification,” he added. (The full interview will air on CNBC’s Squawk Box Monday.)
Note that the reference to “day one” refers to their discovery of the issue. The attack went on for about three weeks.
Support our mission to keep content open and free by engaging with theCUBE community. Join theCUBE’s Alumni Trust Network, where technology leaders connect, share intelligence and create opportunities.
Founded by tech visionaries John Furrier and Dave Vellante, SiliconANGLE Media has built a dynamic ecosystem of industry-leading digital media brands that reach 15+ million elite tech professionals. Our new proprietary theCUBE AI Video Cloud is breaking ground in audience interaction, leveraging theCUBEai.com neural network to help technology companies make data-driven decisions and stay at the forefront of industry conversations.