 SECURITY
SECURITY
 SECURITY
SECURITY
 SECURITY
SECURITY
Apple Inc. today previewed a new security feature that automatically locks down system functionality that could be hijacked in “highly targeted cyberattacks.”
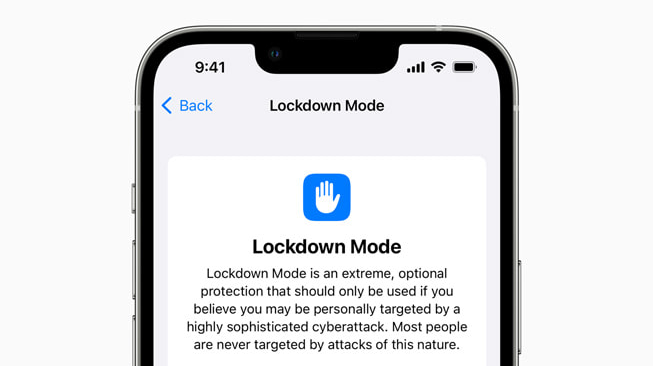
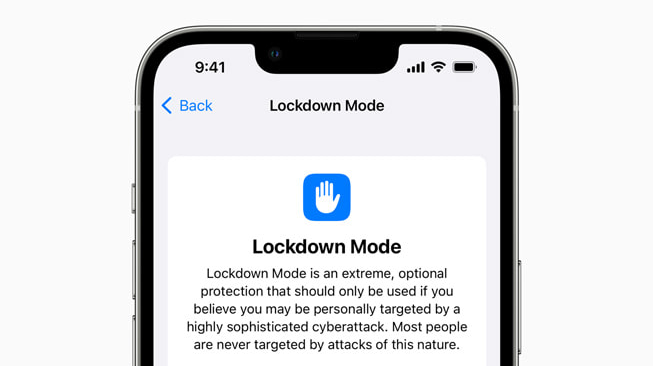
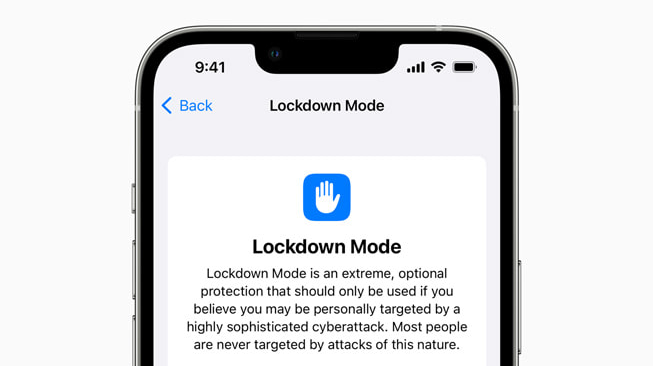
Called Lockdown Mode, the feature, described by Apple as a “groundbreaking security capability,” offers specialized protection to users who may be at risk of highly targeted cyberattacks from private companies developing state-sponsored mercenary spyware. The new service is optional and is targeted at a very small number of users who face grave, targeted threats to their digital security.
Lockdown Mode will be available in iOS 16, iPadOS 16 and macOS Ventura and offers several protections. When enabled, the feature will block most message attachment types other than images. Some features such as link previews are also disabled. Certain web technologies, including just-in-time JavaScript compilation, are disabled unless the user excludes a trusted site from Lockdown Mode.
With Apple services, incoming invitations and service requests, including FaceTime calls, are blocked if the user has not previously sent the initiator a call or request. Wired connections with a computer or accessory are blocked when an iPhone is locked. Configuration profiles cannot be installed and the device cannot enroll into mobile device management while Lockdown Mode is turned on.
“Lockdown Mode is a groundbreaking capability that reflects our unwavering commitment to protecting users from even the rarest, most sophisticated attacks,” Ivan Krstić, Apple’s head of security engineering and architecture, said in a statement. “While the vast majority of users will never be the victims of highly targeted cyberattacks, we will work tirelessly to protect the small number of users who are.”
While Apple primarily pitches the idea using general terms, they’re not shy in holding back on whom the feature really targets, citing controversial Israeli spyware maker NSO Group Ltd. by name.
NSO Group has been one of if not the most controversial cybersecurity companies of recent times. The company’s Pegasus spyware is a form of software that uses zero-day or unpatched exploits to infect mobile devices. The software can breach mobile devices without requiring a user to perform any action and can infect most versions of iOS and Android.
Apple has tried to address the exploits used by Pegasus in the past, such as a September release that addressed the “Forcedentry” exploit. However, NSO Group has a reputation for a reason: The company continues to find new ways for Peagusus to access devices, including iPhones.
Previous exploits used by the like of NSO’s Pegasus and other similar spyware packages have involved sending unsolicited messages to gain access to a targeted device, in some cases not even requiring the message to be opened. That’s where Lockdown Mode steps in, blocking the messages before they can run malicious scripts and take over the device.
Apple intends to make Lockdown Mode generally available in fall.
Support our mission to keep content open and free by engaging with theCUBE community. Join theCUBE’s Alumni Trust Network, where technology leaders connect, share intelligence and create opportunities.
Founded by tech visionaries John Furrier and Dave Vellante, SiliconANGLE Media has built a dynamic ecosystem of industry-leading digital media brands that reach 15+ million elite tech professionals. Our new proprietary theCUBE AI Video Cloud is breaking ground in audience interaction, leveraging theCUBEai.com neural network to help technology companies make data-driven decisions and stay at the forefront of industry conversations.