 INFRA
INFRA
 INFRA
INFRA
 INFRA
INFRA
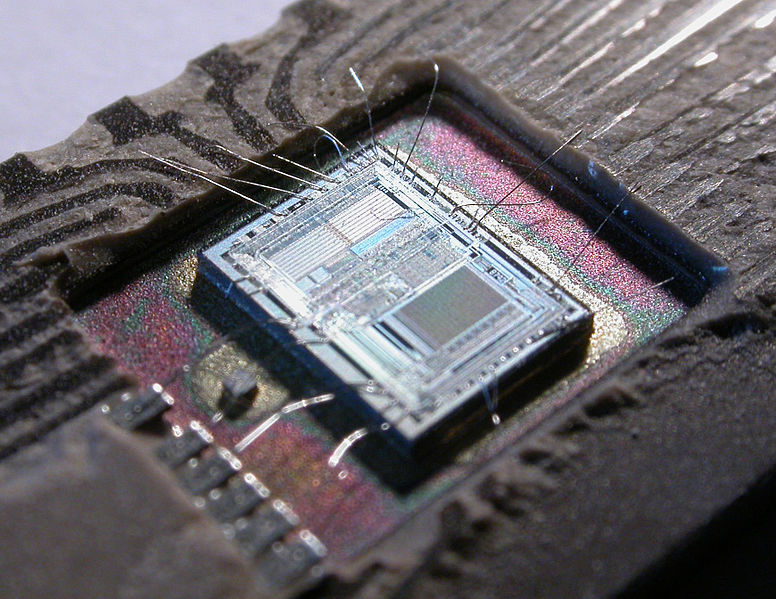
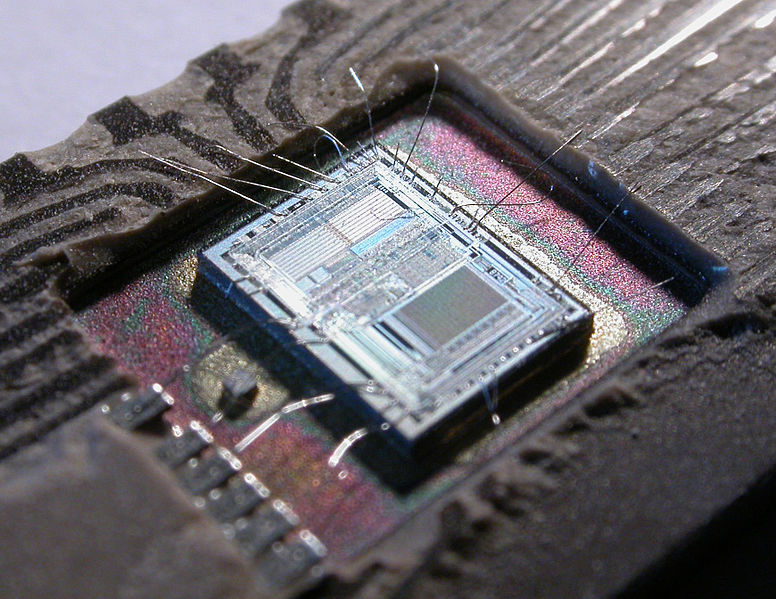
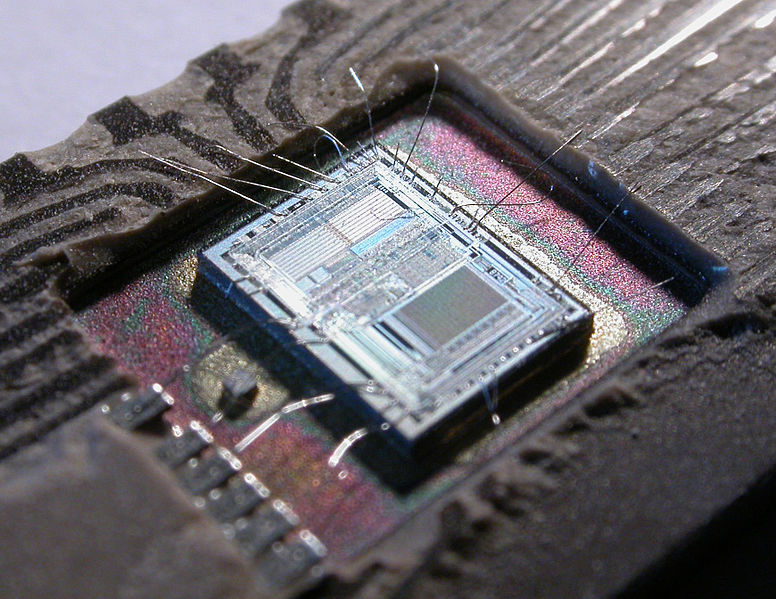
Intel Corp. has issued a patch for a security vulnerability that allowed remote code execution in all of its chips manufactured from 2008 on.
The vulnerability in its chips from those code-named Nahalem to today’s Kaby Lake, stems from a flaw in Intel Active Management Technology, Intel Small Business Technology and Intel Standard Manageability firmware versions 6 to 11.6. It allows an unprivileged attacker to gain control of the manageability features provided by the products.
Intel’s AMT is a feature in its processors that allows organizations to remotely track, manage and secure whole fleets of connected computers — for example, allowing them to monitor and repair digital signage and checkout systems at remote locations such as schools, offices and retail stores.
According to a security advisory published by Intel, the vulnerability provides two routes of access for a would-be hacker. One allows a hacker to gain system privileges to provisioned Intel manageability SKUs, or machine identifiers, in AMT and ISM. The second vector would allow an unprivileged local attacker to provision manageability features to gain network or local system privileges on Intel manageability SKUs with AMT, ISM and SBT.
Put more simply, if AMT is provisioned on a computer, hackers with access to a network the computer is on can access AMT’s controls to hijack the computer. If AMT isn’t provisioned, a hacker can still potentially exploit the bug to obtain admin access.
The tech news site Semiaccurate, which claims to have discovered the vulnerability five years ago and has been trying to get Intel to fix it ever since, claims there is no Intel box made in the last nine years that isn’t at risk. Intel disputes this, saying that the vulnerability affects business and server boxes that have vPro products including ISM, SBT and AMT present and enabled and that “this vulnerability does not exist on Intel-based consumer PCs.”
Intel provides instructions on how to deal with the vulnerability, starting with ascertaining whether a computer ISM, SBT and AMT present, ascertaining whether the system has impacted firmware and a final check to see whether a system manufacturer has provided updated firmware. If so, it will install it. In the event a firmware update is not available from a system manufacturer, disabling or removing the Windows Local Manageability Service can also mitigate the vulnerability.
Support our mission to keep content open and free by engaging with theCUBE community. Join theCUBE’s Alumni Trust Network, where technology leaders connect, share intelligence and create opportunities.
Founded by tech visionaries John Furrier and Dave Vellante, SiliconANGLE Media has built a dynamic ecosystem of industry-leading digital media brands that reach 15+ million elite tech professionals. Our new proprietary theCUBE AI Video Cloud is breaking ground in audience interaction, leveraging theCUBEai.com neural network to help technology companies make data-driven decisions and stay at the forefront of industry conversations.