 SECURITY
SECURITY
 SECURITY
SECURITY
 SECURITY
SECURITY
The RSA Conference takes place in the last week of April this year at a time when the industry is at a crossroads.
Where once it looked as if the security industry would be shielded from macroeconomic conditions, the past year has been painful for many investors, with some exceptions – most notably those investors who stuck with Palo Alto Networks Inc. and Fortinet Inc. That said, Q1 saw a rebound in tech but for the most part cyber lagged. The tech rally was largely attributable to an uptick in semis, a leading indicator in normal times. But these aren’t normal times and RSA gives us a nice opportunity to assess the situation in the market.
In this Breaking Analysis, we’ll update you on the latest trends in the market and what to expect at RSA this year. We’ll also share the latest Enterprise Technology Research spending data and drill into the areas of cybersecurity that are seeing the most action. As always, we’ll highlight those companies with the strongest (and weakest) momentum and close with a look at some of the emerging technology players in security that might be ripe for acquisition. To do all this, we once again welcome in our colleague Erik Bradley from ETR.
Below is a rundown of some themes we expect to hear at RSA this year:
As we intimated at the top, no sector is safe from the economy, including cloud and cybersecurity, two sectors that are typically less affected by negative spending sentiment.
Zero trust is now a thing, not just a bunch of mumbo-jumbo marketing. It’s becoming a software-defined architecture that is accelerating digital.
At RSA, we’re going to hear a lot about artificial intelligence. The reality is AI is going to be embedded in platforms, and while there will be a lot of focus on automation, it’s unclear how foundation models such as GPT will be deployed by defenders. There’s little doubt that attackers will use GPT to develop more sophisticated and better-written phishing techniques and increasingly clever evasion methods. As well, adversaries will use AI to better target high-value assets and sniff out those that are most exposed.
We’re hoping to hear about the end of passwords.
Endpoint detection and response, or EDR, is moving to extended detection and response, or XDR, and leading companies are trying to get ahead of the game and lead in technology, marketing and thought leadership. This shift can be extremely disruptive to many existing segments, including vulnerability management, log management, event management and the like.
Security is an issue that has become top of mind across a company. It’s being embedded in the culture of organizations and no longer the domain of just the SecOps or information technology teams. Developers are more involved, via shift left principles, the boardroom has been hyper-focused on security for nearly a decade, and every employee and partner in the ecosystem is tuned in.
We’re also going to talk about today, and no doubt see at RSA, a spate of emergent security players. Despite the overcrowding in the marketplace, the funding boom of the late 20-teens and early 2020s has created even more cybersecurity companies and solutions. And we expect to hear about more potential acquisition activity at RSA.
Finally, in a shout-out to the tongue-and-cheek play on words by RSA Security LLC Chief Executive Rohit Ghai, identity remains a key subsegment in cybersecurity. Governments are calling for better security and pointing fingers at corporations. The crypto banking crisis has resurfaced discussions of KYC, Know Your Customer, and reputations are being called into question. As such, it begs the question: Is the industry facing an identity crisis?
Erik Bradley discussed the evolution of zero trust in the context of the RSA conference. Initially a marketing buzzword, zero trust has transformed into a software-defined approach to security, becoming a top priority within the community. Drawing a parallel with open generative AI and large language models, Bradley suggests that though they may currently be considered hype, they are likely to follow a similar trajectory and integrate into the security landscape.
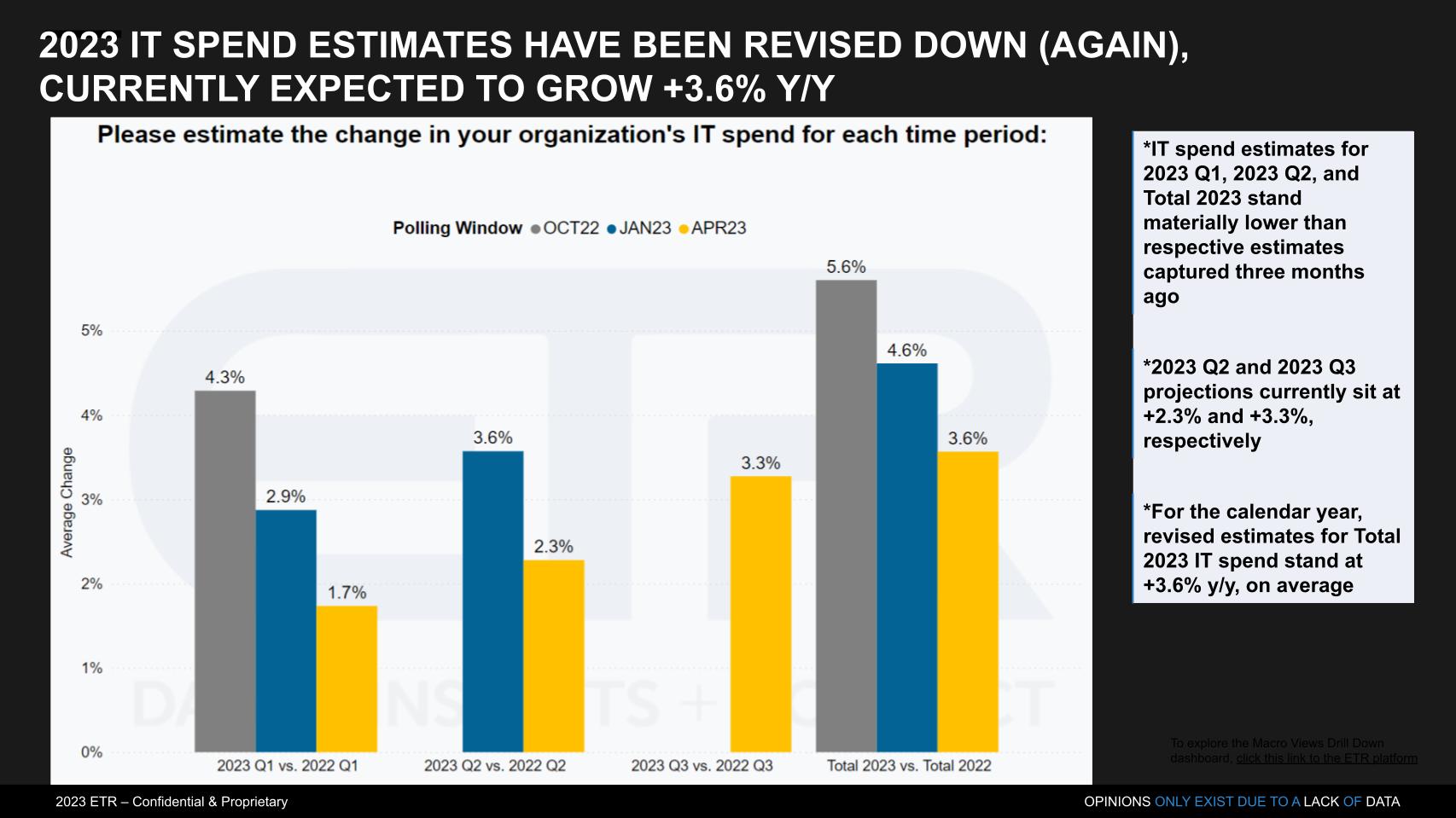
We entered 2023 with IT decision makers expecting 5.6% spending growth and we’re now down to 3.6% overall, as shown in the chart below. The second quarter is looking even more tepid with a 2.3% expected growth rate relative to 2022. The good news is ETR’s most recent spending survey had about 1,700 respondents, a new record. The bad news is that the data is probably better than it has ever been and the outlook keeps getting more negative.
Bradley added the following color:
The more people we survey, the worse it gets, right? So I know Gartner came out recently with a 5.5% [growth for the year]. Our data’s showing around 3.6% across the board. But one of the things that we can do is break this down by separate demographics, whether that’s region, whether that’s industry vertical or size. And something that’s interesting to point out here is that the bigger the company, the less you plan on spending. So the highest spend for next year is actually with small organizations whereas the Fortune 100 respondents are planning on growing less than 1% of their budget. And I think it’s just really interesting to note. And I don’t know if that’s because smaller players are catching up or larger companies are just being a little bit more cautious. But it is interesting to note. And in addition, we’re also seeing that energy and utilities, the type of industry that we used to call a dividend stock or a conservative type of name, they are the highest spenders as well. So even though the data’s coming down across the board on an aggregate basis, there are some pockets of spend, most importantly, in the small organizations.
Erik Bradley explains the spending data in detail.
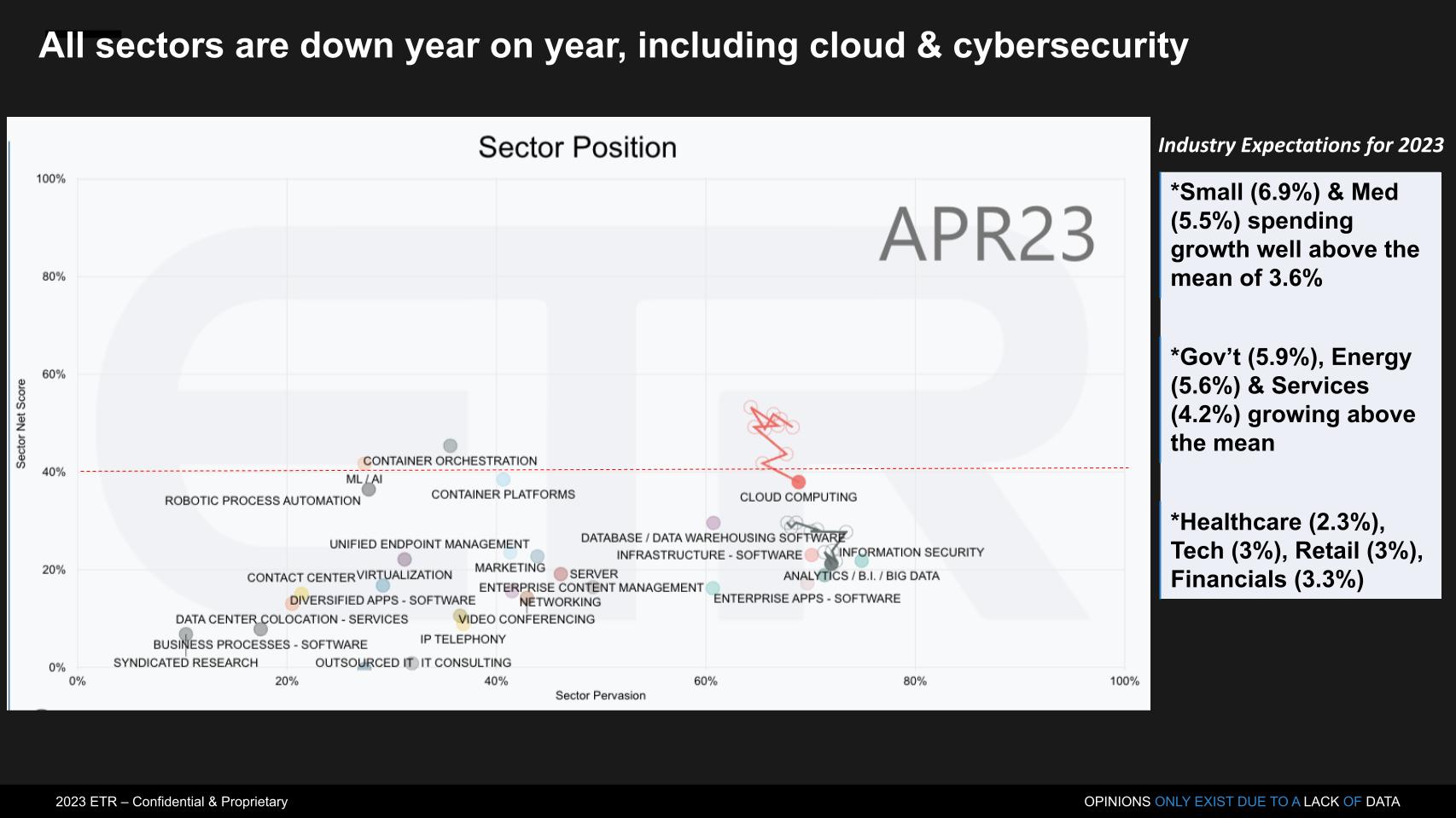
The chart above shows Net Score or spending momentum on the vertical axis and the presence in the data set on the horizontal axis. Every sector is down, including cloud and cyber, which is shown by the squiggly lines indicating the position of those two sectors over the last several surveys. There are some brights spots, particularly small and medium businesses, energy companies and – of course the government continues to spend. But healthcare, tech, retail and financials are all below the mean.
Bradley adds the following color to this data:
A couple of things: On the government… It is passing legislation that they have to catch up on security. So that spend is also going to help. And on the sector basis, it really is kind of scary, because it’s across the board. Generally in years past, we’ve lived through a lot of tough times and we’ll see one or two areas get hit or a couple that stand out, but nothing seems immune to the current environment right now. Normally cloud spending is immune, normally security spending is immune, and even though our data shows them as the highest priorities, the overall spending still coming down.
[Erik Bradley explains the sector spending compression in enterprise tech].
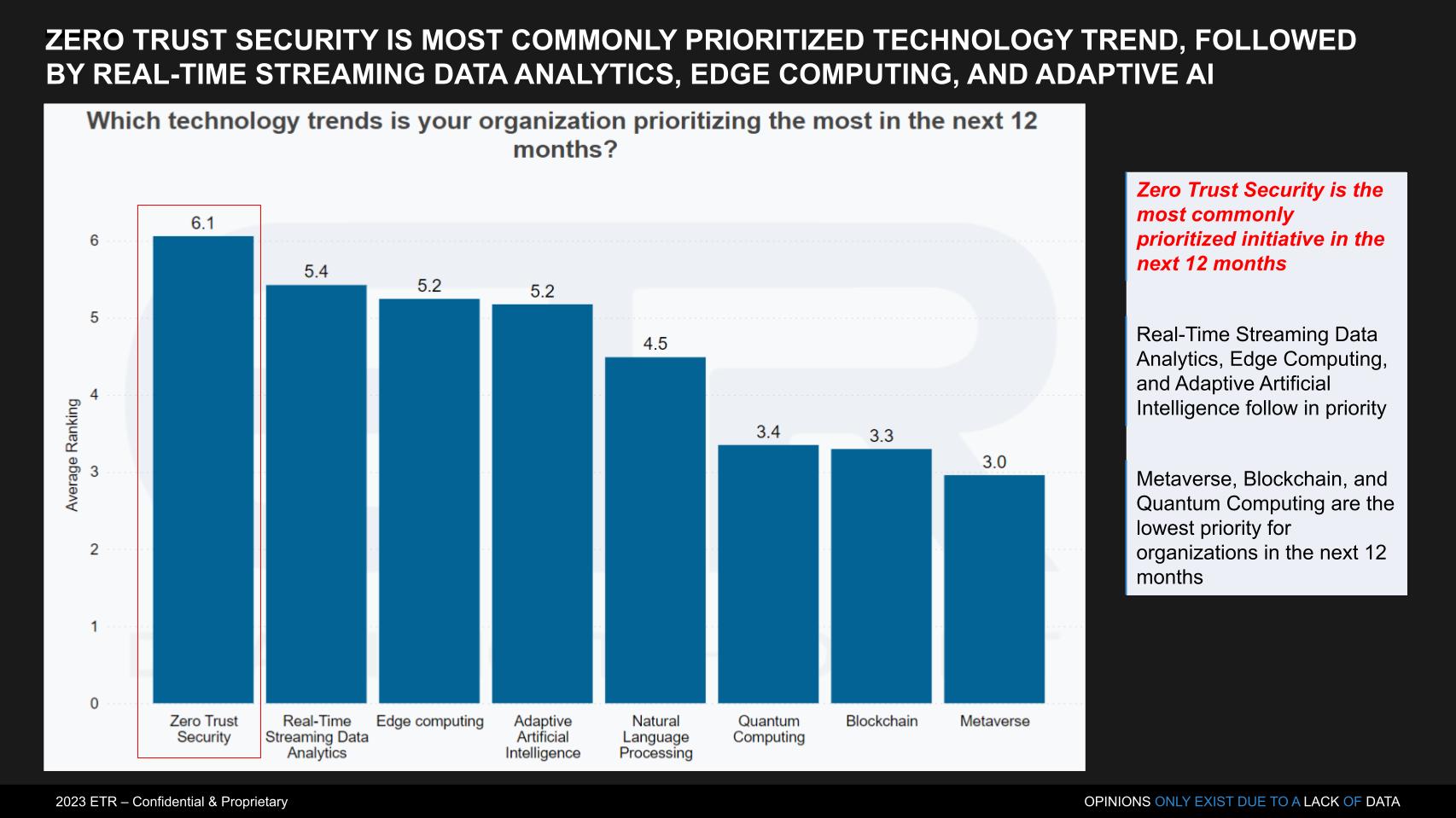
Followers of Breaking Analysis and ETR know that we’ve often shown data citing security as the No. 1 spending priority. This past survey, ETR chose to change the way it asked this question. It came out of an initial deep dive with chief information officers and chief information security officers to identify the key trends and ETR then used those as the basis for the broader survey. According to Erik Bradley:
We decided to change this question up a little bit. And this is based on a top-trends interview series that I conducted back in January where we took 10 CIOs and CISOs, asked them what their top trends were. We could all see that on the ETR platform if you want. What we did is we took those top trends and then put them as the ranking order. But lo and behold, security was number one. Again, this time, zero-trust security. And then we also dug down a little bit deeper later in this survey to find out exactly which aspects of security were of the most important and the highest priority, which we can dig into. Again, to your earlier point, this is not hype, this is not a philosophy, this is real application that CISOs are employing.
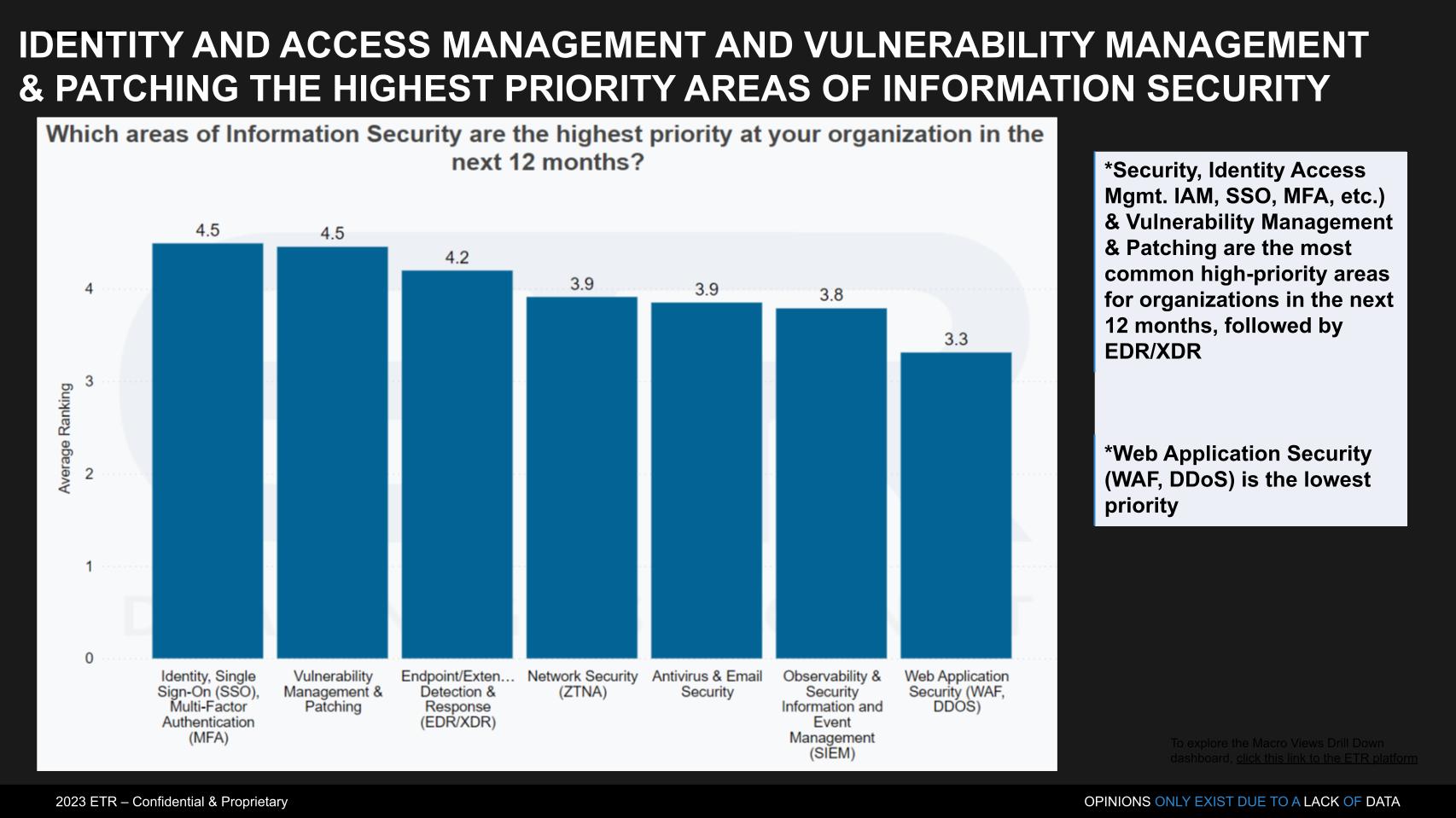
According to Bradley:
We decided to go one level deeper on this one. And we know security is the No. 1 priority, but that data point was just getting stale. So we said, “OK, let’s figure out which ones there are.” And identity access management as No. 1 was not surprising. What was surprising and jumped off this page to me was vulnerability management being tied for No. 1 priority. We think of that as just basic hygiene. That’s security scanning, patching, that’s not something that we think of as the highest priority and the sexiest. But right now in all the conversations I’m having, constantly vulnerability management is coming up. One of the things we’re also seeing is right next to it is the EDR moving into XDR. And this is probably the biggest trend, and I expect to hear a lot about it at RSA.
This EDR moving to XDR can really be disruptive to everything. It can be disruptive to vulnerability management, it can be disruptive to log management, like SIEM and the observability players, like Elastic and Datadog. If you are doing XDR properly, all of that data telemetry is going to be coming into that and therefore they can disrupt a lot. You can take a lot of budget out. I’ve heard some CISOs tell me that CrowdStrike and SentinelOne have come to them and said, “Get rid of Qualys, get rid of Tenable, get rid of Rapid7, I can do it for you.” Now they’re not ready to go ahead and do that, but that’s the rhetoric that’s happening in the marketplace right now. So it’s something to really keep an eye on.
Below we show the same two-dimensional graphic with spending momentum or Net Score on the Y axis and overlap or presence within the data set on the X axis, plotted based on the number of mentions. The red dotted line indicates highly elevated spending velocity on a platform. On the insert in the bottom right, we’ve cited those companies near or above a Net Score of 40% – Microsoft, Auth0, CrowdStrike, CyberArk, Okta (which owns Auth0), SailPoint and Zscaler. The names above the red line continue to get compressed as the market softens.
Microsoft stands out as the leading in presence and yet maintains the highest spending momentum. Quite remarkable. Cisco Systems is also large but doesn’t have the spend velocity on its platform as some others, including Palo Alto Networks, which has a strong presence and very good spending momentum on its products. CrowdStrike is also notable on the vertical axis. Its business rebounded last quarter and it just did a deal with Dell Technologies, which is strong in small business. Given the stronger spending momentum from smaller companies that could bode well for the company.
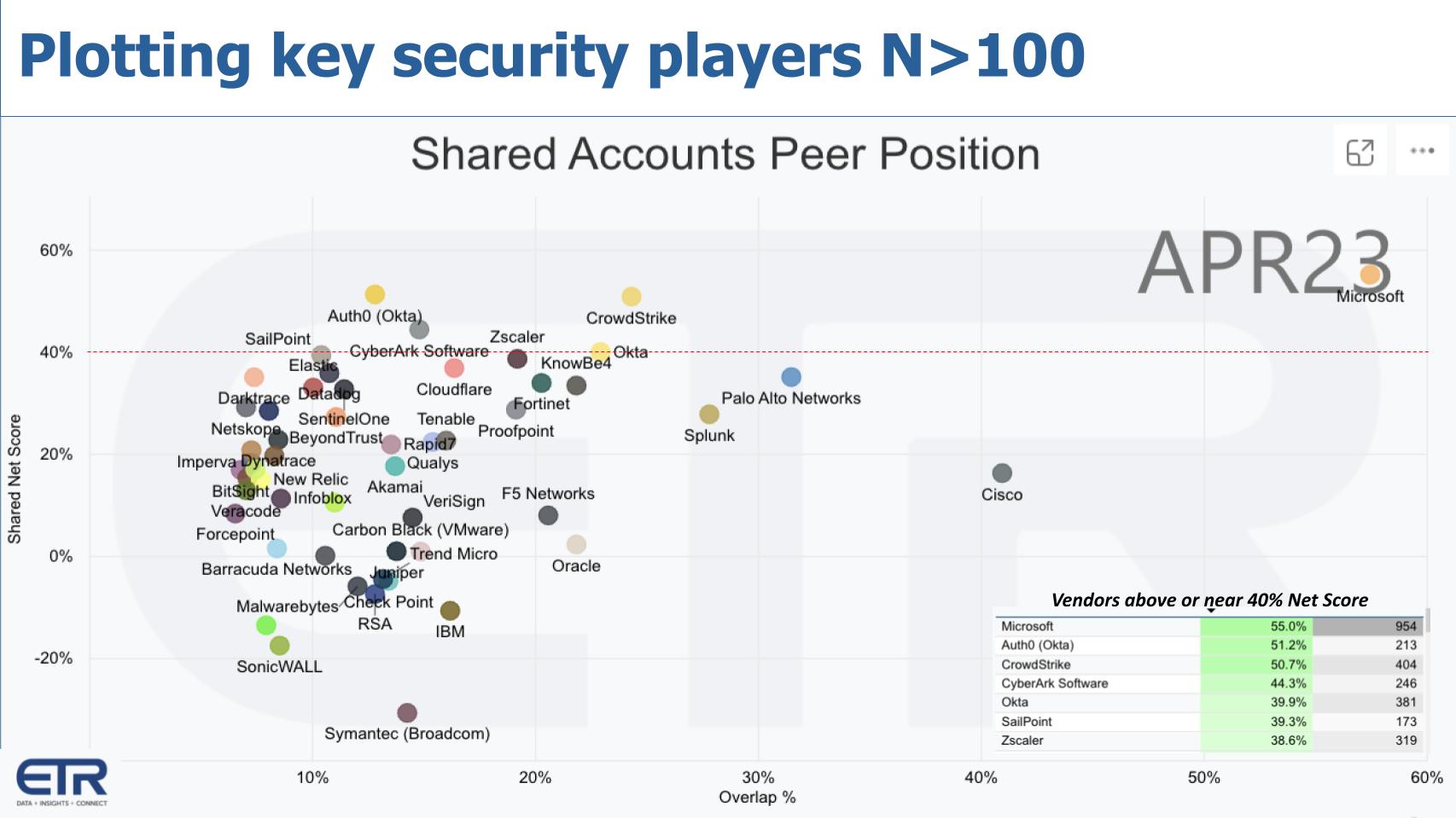
Bradley had the following to say about this data:
We’ve got a very crowded marketplace. Many of these names are viewed as niche or point solutions and they could be best-of-breed, but I want to call out just that one name that’s hiding in the top right corner there, Microsoft. Now are they the best at everything? No, they’re not. But they’re getting pretty good, they’re getting good enough. And I had one CISO recently who told me, “Obviously, I’d love to have something like Splunk or Elastic or SentinelOne, but if I just need a workmanlike job, I’m going to go to Microsoft, because it’s better for me from a cost perspective, it’s better for me from a human management perspective.” And Microsoft just continues to do the job well. And now with generative AI and large language models, I’m really interested to see what they’ll do. They’re still going to be a dominant factor in security. But overall spending is coming down, that’s the backdrop.
So I’m not so concerned to see these Net Scores dipping below the 40% level. The ones that you consider best-of-breed are still up there. You know, obviously the CrowdStrikes, the Zscalers, the Oktas, the SailPoints, they’re still up at that level. And I think if we see budgets return, we’ll see those Net Scores go back up as well. I’m not as worried about the drop. It really is something that you shouldn’t expect in the spending environment and the concerns we have on a macro basis.
Listen to Erik Bradley and Dave Vellante riff on some of the top security players.
A few years ago, we came up with a methodology that underscores the capability of ETR’s data platform. It’s simple but really powerful. What we’ve done below is take the top 20 companies in the survey with at least 100 responses on their platform and sort them. On the left we sort by Net Score and the right by the number of Ns in the data set. The red dotted line is the top 10 on each cut.
If a company makes the top 10 in both spending momentum and presence in the data – that is, Shared N — they get four stars. And we’ve given two stars for honorable mention if the company makes the top 20 in both.
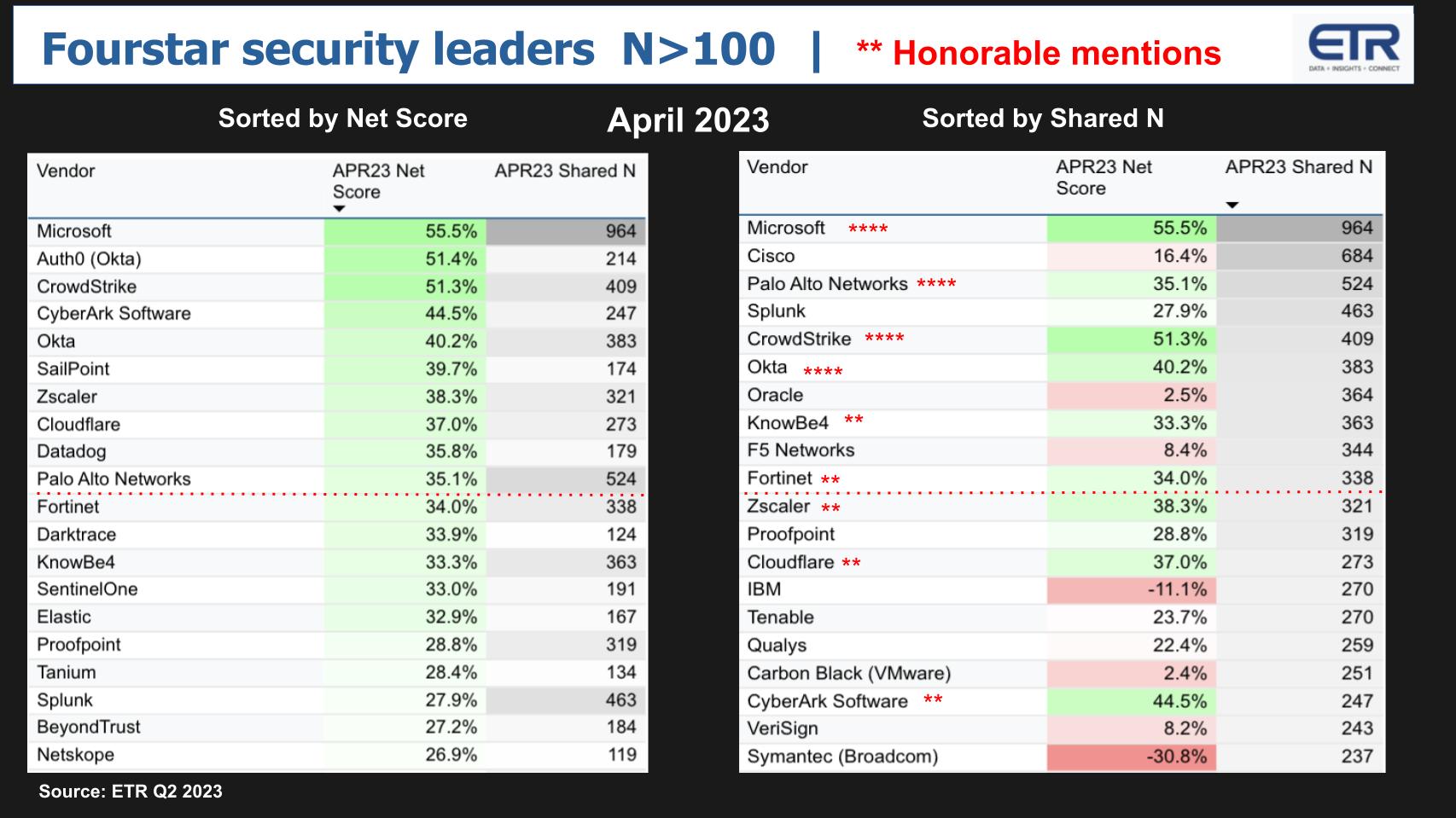
Microsoft, Palo Alto, CrowdStrike and Okta each get four stars.
Fortinet just missed so should probably get three stars but KnowBe4, Zscaler and Cloudflare are right ther, and CyberArk is strong – also getting two stars with a 45% Net Score — it just needs a bit more market presence to get to that four-star level.
Bradley summarizes this data as follow:
First of all, I love it. I play with this data all day long and I’ve never done this before, so I might be stealing it from you, Dave. I think it’s fantastic. Couple of names here that really jump out. I think KnowBe4 is just doing fantastic work and people are using them for the training aspect. And as we all know with all of these attacks, it almost always comes down to some human miss. Training is imperative and KnowBe4 is in a great spot for that training. So I think they deserve a quick call out. The other one here that we have to talk about is Cloudflare. I mean, Cloudflare is just absolutely amazing. They’re in great position, because people are already using them. If you have any application, if you have any web application presence, they’re already being used, and they are just across the board. So they’ve got also denial distribution of service, they’ve got the DDoS, they’ve got web access firewall, they’ve got balancing, they’ve got bot protection, and everything we hear about Cloudflare are the people that are using them are extremely pleased with the service and they just kind of keep adding more and more and more security.
And they’re really one of these names that just, you can’t give ’em enough credit. They’re becoming more pervasive in the enterprise, their net score, their spending is off the charts. And I think they’re going to be more inquisitive going forward.
Listen to Erik and Dave riff on the players and drill into Cloudflare a bit.
Let’s turn to some of the privately held companies in cybersecurity. ETR has increased the frequency of its emerging technology survey or ETS over the past year and it’s a treasure trove of data. The chart below plots Net Sentiment on the Y axis, which is a measure of intent to engage (evaluate or use). On the X axis is Mind Share measured by Ns in the survey.
These are nonpublic, emerging companies that ETR specifically tracks with more than 1,400 IT decision makers. It’s surprising that in such a crowded market there’s still room for so many emerging companies. As well, so many are well-known based on this Net Sentiment data on the vertical axis.
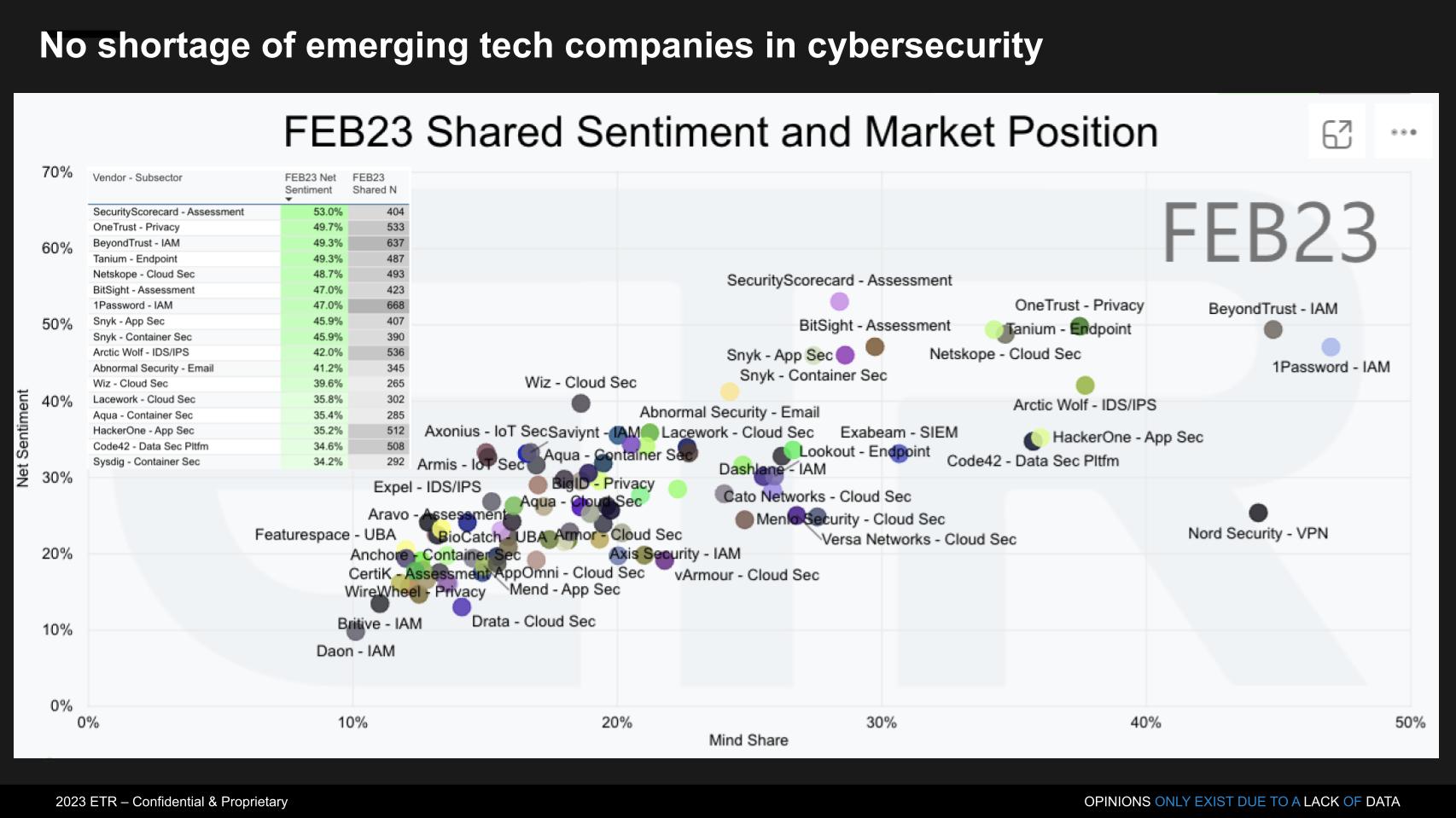
Bradley explained the data as follows:
ETR was launched as a financial services research company. We started off researching the public tech companies, but obviously privates and venture-backed companies became so big that we needed something for them as well. And now it’s really just more about the enterprise tech companies themselves needing this competitive intelligence data. So you’re right, we really have doubled down on this emerging side. What really jumps out to me is I have a different view over here on my screen I’m looking at, which is just the overall plans to evaluate. And the No. 1 and No. 2 names are the same, they’re both Snyk. And that’s because we follow them in container security and application security. And the reason I want to bring it up is because we talked earlier about vulnerability management, the XDR players trying to encroach on them, the other issue with vulnerability management is they weren’t born cloud-native, they were born with more old-fashioned types of network and on-prem technologies.
[Snyk] is cloud-native. These guys work in containers and cloud architectures. I don’t think they’re going away. There’s a lot of names on this list that I just think are just dominating in their space. It’s only a matter of time before they either get taken out or go public themselves. So there’s a lot of data here and this data can be predictive. We’ve predicted acquisitions before by crossing this data with the public TSIS data and really seeing where the overlap is with the end user base.
Erik Bradley explains the Emerging Tech Survey results.
The chart below unveils another really powerful capability in ETR’s data. What we’re doing here is taking the privately held companies in the ETS data and picking some possible acquiring companies. For the acquirers, we chose Cloudflare, Fortinet, Palo Alto Networks, Cisco, IBM, CrowdStrike, Zscaler, Microsoft, Google, Amazon Web Services, CyberArk and Okta. And we crossed the data to identify the overlap between these publicly traded companies in the core TSIS data with the emerging tech companies to highlight possible acquisitions.
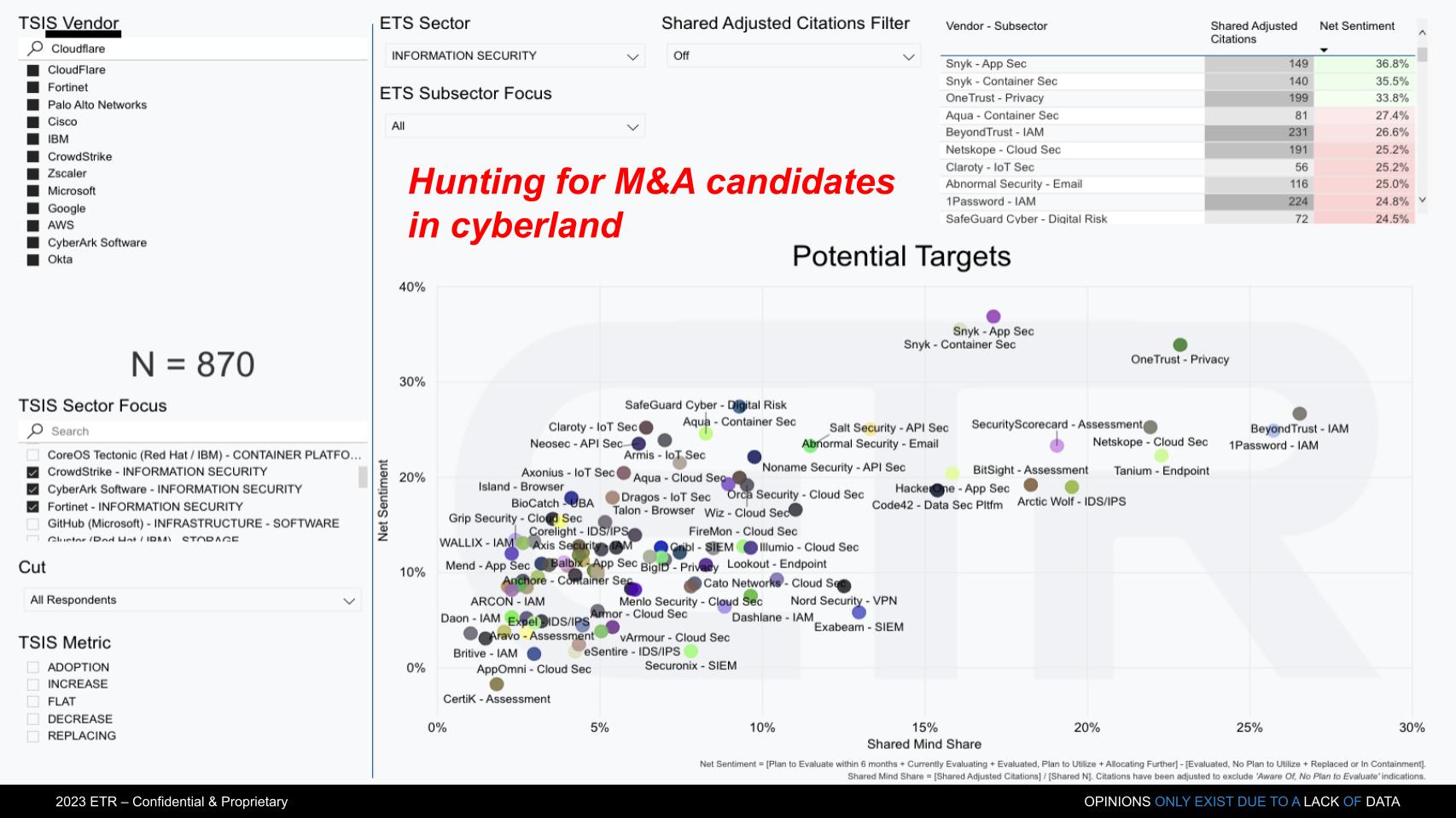
Bradley explained:
What you’re looking here on the left side is of those 870 respondents, that’s people that took the TSIS and cited spending for these companies over there on the left. Then among those 870 we say, “OK, which companies on the emerging or private side are best positioned?” Therefore basically whether it’s tech stack alignment or disruption, for some reason, there’s a very strong correlation in their accounts, meaning you have the same customers basically. So they’re either disrupting you or there’s some actual contingency there where the tech stack benefits each other and they correlate.
When we actually look at the numbers here, again, Snyk jumps out at me, Snyk jumps out right away. A name like Salt Security that does API security, so important right now, they jump out at me. Abnormal is in email security. We haven’t seen email security change in so long and we’re still using Proofpoint. And right now, as you mentioned earlier in the show, I truly expect generative AI to increase the efficacy of phishing campaigns. All of us need to ratchet up our email filters. So these are all names that should be looked at and I think the big companies with cash are looking at ’em ’cause there’s another factor at play.
SVB just failed. Private equity funding isn’t what it used to be, we’re in a bad macro environment. If these guys need cash, they’re not just going to go back and do a Series D at the same valuation, that world is over for right now. But you know who does have the cash? Some of the public companies, they’re sitting on it. And there’s people out there that are used to acquiring, like a Palo Alto, like a Cisco, like others. They are used to making acquisitions, they have cash, and there’s a lot of great companies out there for the taking.
And in the past, we’ve actually predicted, just to name two of them, Palo Alto taking out Twistlock and Okta taking out Auth0 through this exact screen that you did. I give you an A+ on this screen, Dave. You did a great job on this model.
In the latest ETR Drill-down survey, CIOs and IT decision makers were asked if their firms are evaluating large language models and, if so, for what purpose?
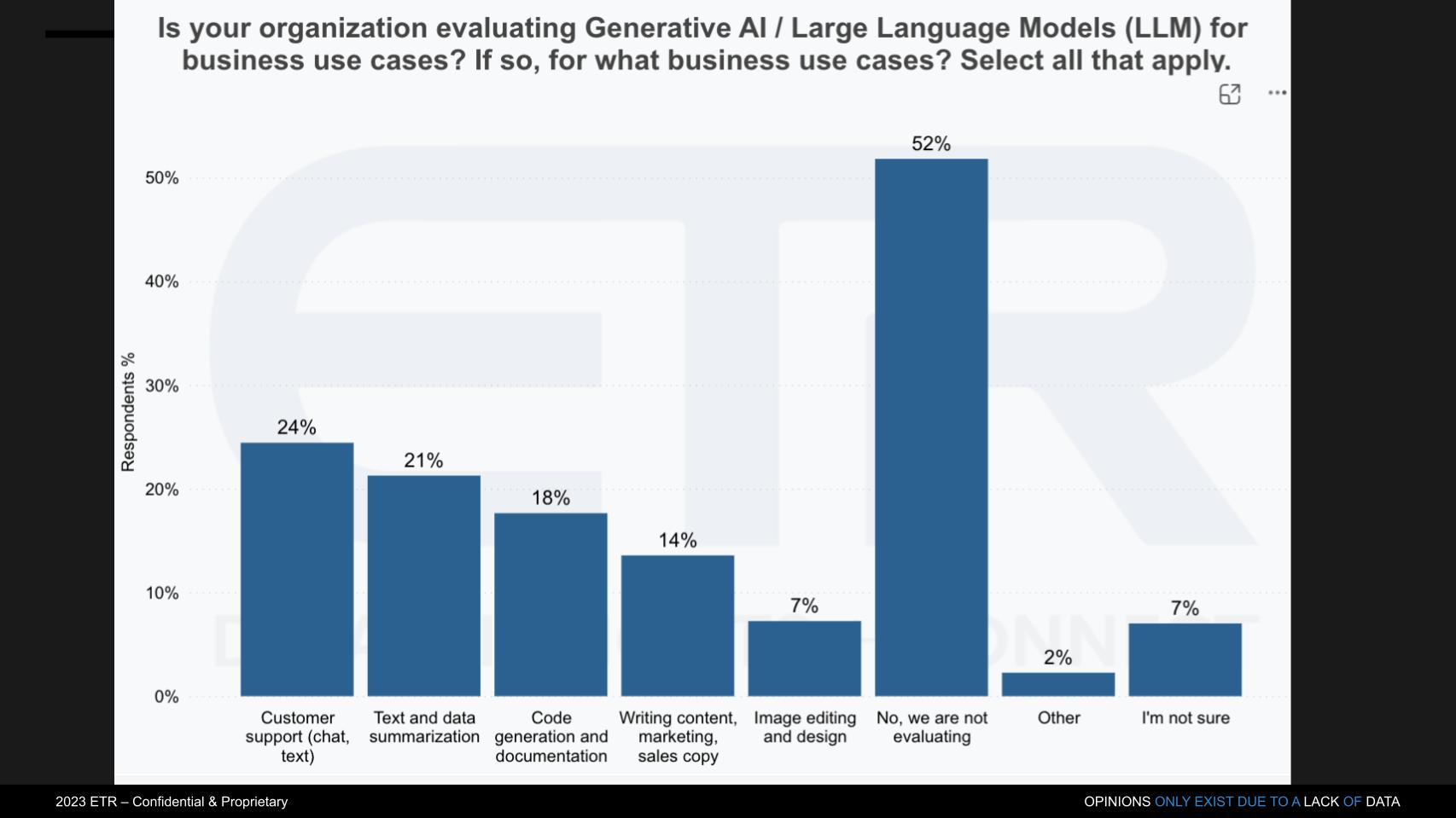
The first thing that strikes as odd is that half the sample said they’re not evaluating. Which is surprising. It’s likely someone at the firm is looking at GPT. But the more interesting stats are the use cases. Chatbots of course and summarizing text – both strengths of ChatGPT. Writing code and documentation, sales and marketing copy and the like.
But not much happening in the context of cybersecurity based on the initial scan of the market.
We asked Bradley what he makes of the hype over the last 120 days or so as it relates to ChatGPT, Bard, AWS announced its large language model strategy last week. Here’s what he said:
In early March when it came out, I was fortunate enough to get called by a journalist at the Wall Street Journal and worked with him on a report. We did a flash survey. And what we found out with that survey was right now, it’s more hype than anything. People are scared of it. Even my own company had to come out with a policy telling our employees, “Hey, you’re not allowed to throw our data on there, because once you throw your data on there, it’s not ours anymore.” So people are still really concerned about the guardrails around it. Now the issue is you’re not going to avoid this buzz. This is the ultimate shadow application. People are going to go and try it and use it, it’s going to creep in. Therefore, I believe large enterprises are going to trust a partner more than going to a straight up ChatGPT-type of OpenAI.
I think they’d rather see it worked in with Microsoft, they’d rather see it worked in with Salesforce, or AWS, or GCP. And we’re hearing more and more announcements about that. I think that’s the way it’s going to get into the enterprise. But I do want to state that also when we did the ETS, OpenAI had the largest-ever debut score on people saying they plan to evaluate it, the highest ever. So if they can convert that plan to evaluation into actual customers, it’ll be really interesting to see in the next ETS. I want to see if that number moves. But specifically to this drill-down, what we’re seeing here is it’s really more about customer support than it is about creating its own. We did not specifically ask about security in here, but I’ve had multiple people tell me, and I can even quote one, “Once we get more leverage out of AI into RPA, it’s going to help close the gap in cyber risk models specifically. Right now it’s a buzzword, but the more and more intelligence we get in, it’s going to become a true measure in terms of our risk management.” That was a direct quote from a CISO at a global 2000 organization when I asked them about this in general. It’s just a matter of time, Dave. It’s going to happen.
Erik Bradley comments on the adoption of LLMs in enterprise IT.
Before we finish, we want to give you the rundown on theCUBE at RSA:

We were approved by RSA Conference as a media partner this year and we’ll be on Broadcast Alley in Moscone West. You can catch the action on the website we’ve set up for the event. We’ve lined up CISOs, cyber experts and analysts, and we’re going to have a great show. We’ll have a big crew, so check out the action on siliconangle.com as well, where we’ll have all the news and announcements.
Join us in Moscone West each day. We start right after the keynotes and look forward to seeing you there.
Thanks to Erik Bradley for his ongoing partnership and contributions to Breaking Analysis. Thanks to Alex Myerson and Ken Shifman on production, podcasts and media workflows for Breaking Analysis. Special thanks to Kristen Martin and Cheryl Knight who help us keep our community informed and get the word out, and to Rob Hof, our editor in chief at SiliconANGLE.
Remember we publish each week on Wikibon and SiliconANGLE. These episodes are all available as podcasts wherever you listen.
Email david.vellante@siliconangle.com, DM @dvellante on Twitter and comment on our LinkedIn posts.
Also, check out this ETR Tutorial we created, which explains the spending methodology in more detail. Note: ETR is a separate company from Wikibon and SiliconANGLE. If you would like to cite or republish any of the company’s data, or inquire about its services, please contact ETR at legal@etr.ai.
Here’s the full video analysis:
All statements made regarding companies or securities are strictly beliefs, points of view and opinions held by SiliconANGLE Media, Enterprise Technology Research, other guests on theCUBE and guest writers. Such statements are not recommendations by these individuals to buy, sell or hold any security. The content presented does not constitute investment advice and should not be used as the basis for any investment decision. You and only you are responsible for your investment decisions.
Disclosure: Many of the companies cited in Breaking Analysis are sponsors of theCUBE and/or clients of Wikibon. None of these firms or other companies have any editorial control over or advanced viewing of what’s published in Breaking Analysis.
Support our mission to keep content open and free by engaging with theCUBE community. Join theCUBE’s Alumni Trust Network, where technology leaders connect, share intelligence and create opportunities.
Founded by tech visionaries John Furrier and Dave Vellante, SiliconANGLE Media has built a dynamic ecosystem of industry-leading digital media brands that reach 15+ million elite tech professionals. Our new proprietary theCUBE AI Video Cloud is breaking ground in audience interaction, leveraging theCUBEai.com neural network to help technology companies make data-driven decisions and stay at the forefront of industry conversations.